Groups are an important part of an organization’s Active Directory.
- For sharing information, distribution lists are quite handy.
- For assigning permissions and granting access to resources based on their roles and designations, security groups are indispensable.
When it comes to managing Active Directory groups, small organizations may need to create groups occasionally, but in larger organizations, groups may swirl out of control for reasons such as:
- An organization has many departments and plenty of projects are undertaken by each of the departments. There is a need to create a group for every project and add project teams as members.
- Departments must collaborate with vendors and other third parties on a day-to-day basis. For communication, they need those external users to be part of distribution groups.
In such situations, the group creation activity could grow daily or at least on a weekly basis.
Limitation of MS Tools for AD Objects & Powershell
Microsoft provides the following GUI (Graphical User Interface) tools to create and manage objects, like users, contacts, and groups:
- ADUC (Active Directory Users and Computers)
- ADAC (Active Directory Administrative Center)
But these tools have their limitations, like:
- They do not provide the option to update many attributes during object creation.
- You cannot create multiple objects instantly.
Microsoft provides PowerShell to create and manage objects, like users, contacts, and group via simple cmdlet. You can expand those cmdlets by using the scripting feature to create and manage objects in bulk.
This blog focusses on the creation of group objects. We will use PowerShell commands to:
- Create a single group and update its properties during creation.
- Create bulk groups using PowerShell scripts with the New-ADGroup cmdlet.
Finally, we will take this procedure one step further by using third-party tools to automate the group creation process.
Table Of Contents
-
New-ADGroup – Description
-
New-ADGroup – Syntax
-
New-ADGroup – Parameters
-
Create a Basic Group
-
Create a Group with Description
-
Set Managed By
-
Create a Group in a Specific OU
-
Create a Group with a Specific Group Type and Scope
-
Create a Group using the Properties of an Existing Group
-
Create a Group on a Specific DC or LDS Instance
-
Create Groups in Bulk
-
Create a Group with Other Attributes
-
Create Groups with Imanami GroupID
New-ADGroup – Description
Using the New-ADGroup cmdlet, you can:
- Create group objects in Active Directory.
- Define many properties of the newly created group with multiple parameters provided by this cmdlet.
This cmdlet does not have a parameter for every property of a group but has a unique parameter named “OtherAttributes”, using which you can populate the values for properties that cannot be set by the cmdlet’s common parameters.
The New-ADGroup cmdlet requires the -Name and -GroupScope parameters to create a new group. You can also define the group type as security or distribution using the -GroupCategory parameter. The -Path parameter can be used to specify a specific OU location for the group to be created in.
There are many ways to create objects using the New-ADGroup cmdlet, some of which are as follows:
- You can simply use the New-ADGroup command with the required parameters.
- You can also use an existing group as template for creating a new group. In this way, the new group has the same properties as those of the template group. Use the Instance parameter to achieve this. You can also override some of the unwanted properties of the template group.
- You can use a CSV file to create multiple objects and can set multiple properties using the columns as values for the created groups. The Import-CSV cmdlet can be used in conjunction with New-ADGroup for this purpose.
- First use the Import-CSV cmdlet to collect the group objects with their properties from the CSV file.
- Then, using pipeline, you can pass that information to the New-ADGroup cmdlet to handle group creation.
New-ADGroup – Syntax
The New-ADGroup cmdlet has the following syntax:
New-ADGroup [-WhatIf] [-Confirm] [-AuthType ] [-Credential ] [-Description ] [-DisplayName ] [-GroupCategory ] [-GroupScope] [-HomePage ] [-Instance ] [-ManagedBy ] [-Name] [-OtherAttributes ] [-PassThru] [-Path ] [-SamAccountName ] [-Server ]
New-ADGroup – Parameters
The New-ADGroup cmdlet uses the following parameters.
| Parameter | Description |
|---|---|
| -WhatIf | Provides information about the output of the command before running it. |
| -Confirm | Provides a confirmation prompt before running the command. |
| -AuthType | Used to select the authentication type to use, i.e., Basic or Negative. |
| -Credential | Used to provide alternative credentials to run the command. Default credentials are those of the logged-on user. |
| -Description | Used to populate the description of the group. |
| -DisplayName | Used to set the display name of the group. |
| -GroupCategory | Used to set the group type as distribution or security. |
| -GroupScope | Used to set the group scope as domain local, global, or universal. |
| -HomePage | Used to set the home page attribute value for the group. |
| -Instance | Used to collect information of the template group, which is used to set the properties of the new group. |
| -ManagedBy | Used to set the managedBy attribute value for the group, such as the group owner’s distinguished name. |
| -Name | Used to set the group name. |
| -OtherAttributes | This is an important parameter. Using the -OtherAttributes parameter, you can set the values for those attributes of the group for which there is no parameter available. |
| -PassThru | Using the PassThru argument, you can request output from cmdlets that don’t return anything by default. It’s most frequently used to make sure the cmdlet behaved as you had planned. |
| -Path | Used to provide the distinguished name of the OU where you want to create the group. |
| -SamAccountName | Used to populate the SAM (Security Account Manager) name of the group. |
| -Server | Using this parameter, you can provide the directory server (domain controller or an AD LDS instance) where you want to create the group. |
Create a Basic Group
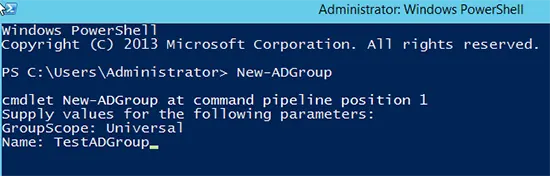
If you only type the New-ADGroup command in PowerShell, the following will happen:
- The command will ask you for the group name.
- The command will ask for the group scope.
- Group type will be “Security” by default.
- The group will be created in built-in OU named “Users”.
It is shown in the following screenshot.
Create a Group with Description
The following cmdlet creates a group with a description:
New-ADGroup -Name “Marketing” -Description “This is a group for marketing people”
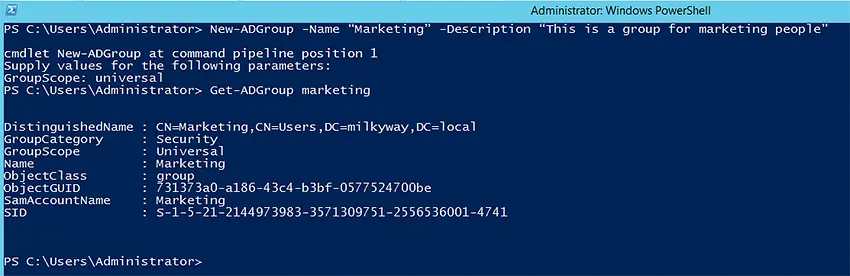
The New-ADGroup cmdlet does not show any output; it only creates the group in AD. You can use the Get-ADGroup command to view the details of the newly created group.
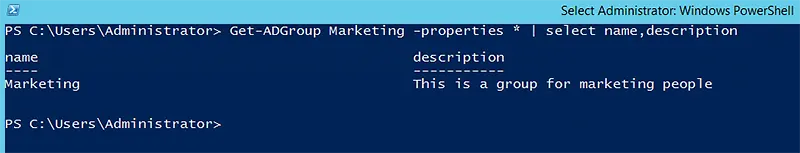
To see the precise attribute detail, such as “Description” of the newly created group, use the following command:
Get-ADGroup Marketing -Properties * | select name,description
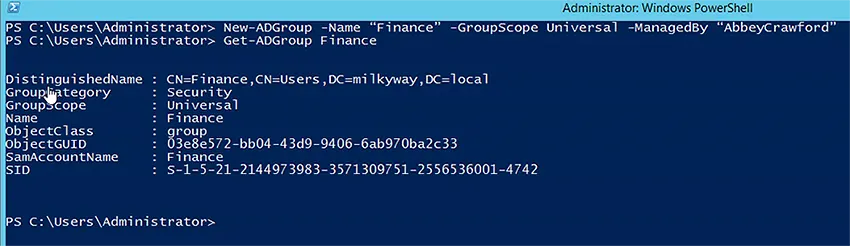
Set -ManagedBy
You can use the -ManagedBy parameter to set the owner of the group. The owner can be a user or a group. This parameter accepts the following as value:
- DN (Distinguished Name)
- GUID (Globally Unique Identifier)
- SID (Security Identifier)
- SAM (Security Account Manager) name
Mostly DN and samAccountName values are used. In the following cmdlet, we have used the samAccountName of the user who will be set in the ManagedBy attribute:
New-ADGroup -Name “Finance” -GroupScope Universal -ManagedBy “AbbeyCrawford”
Create a Group in a Specific OU
You can use the -Path parameter with the distinguished name of the organizational unit as its value, where you want to specifically create the group.
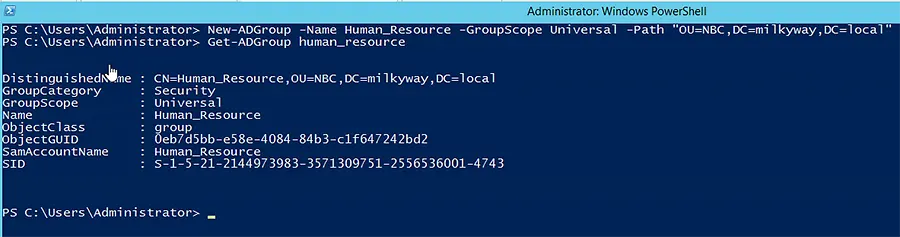
New-ADGroup -Name Human_Resource -GroupScope Universal -Path "OU=NBC,DC=milkyway,DC=local"
The following screenshot shows the output of the New-ADGroup cmdlet, which is obtained using the Get-ADGroup cmdlet.
Create a Group with a Specific Group Type and Scope
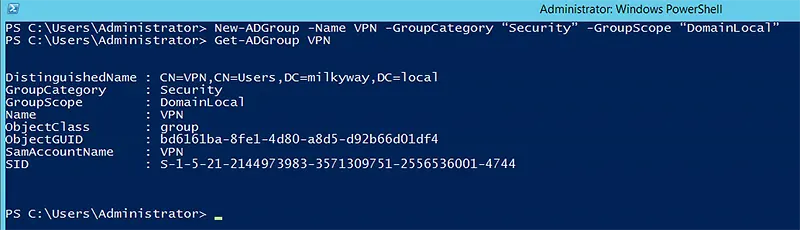
You can create groups with a specifically provided group type and group scope by using the -GroupCategory and -GroupScope parameters respectively.
New-ADGroup -Name VPN -GroupCategory “Security” -GroupScope “DomainLocal”
Create a Group using the Properties of an Existing Group
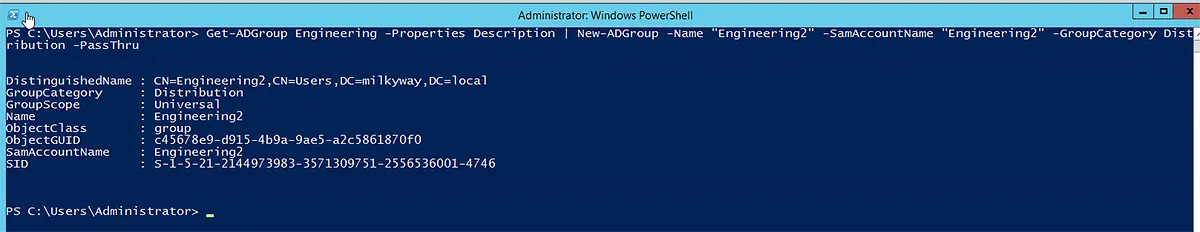
To create a group based on the properties of an existing group, you must first get the existing group’s attributes and then pass them to the New-ADGroup command for creating a new group.
Get-ADGroup Engineering -Properties Description | New-ADGroup -Name "Engineering2" -SamAccountName "Engineering2" -GroupCategory Distribution -PassThru
Create a Group on a Specific DC or LDS Instance
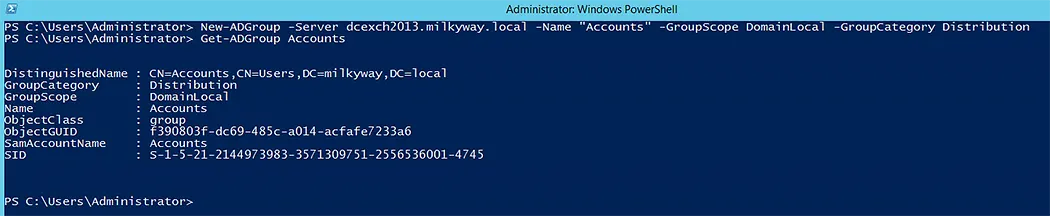
If you have a requirement to create new group on a specific domain controller or LDS instance for the group to be available immediately for use, you can use the following cmdlet to achieve this:
New-ADGroup -Server dcexch2013.milkyway.local -Name "Accounts" -GroupScope DomainLocal -GroupCategory Distribution
Create Groups in Bulk
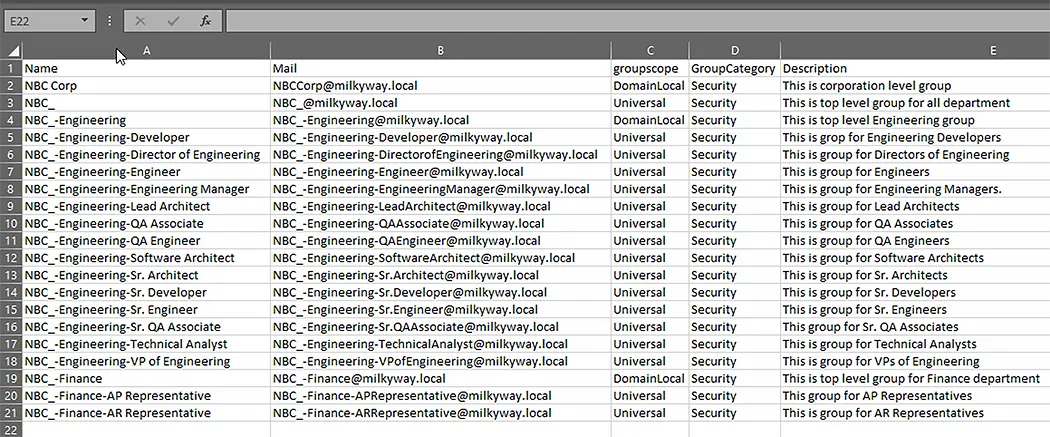
PowerShell enables you to create bulk objects using a CSV file. In the following example, we will create a sample CSV file, which would be used to create groups in bulk using the Import-CSV and New-ADGroup cmdlets in conjunction in a script. Below is the sample CSV file:
$Import_Group = Import-Csv -Path c:\groupslist.csv
foreach ($group in $Import_Group) {New-ADGroup -Name $Group.Name -Path “OU=NBC,DC=milkyway,DC=local” -Description $Group.description -GroupCategory $group.groupcategory -GroupScope $Group.groupscope -Otherattributes @{'Mail'=$Group.Mail}}
The above script will get the contents of groupslist.csv into a variable, and then pass each record one by one to New-ADGroup in a “for” loop. This script does not generate an output, so we have used the following cmdlet to see the newly created groups and their populated attributes:
Get-ADGroup -Filter 'Name -like "NBC*"' -SearchBase "OU=NBC,DC=milkyway,DC=local" -Properties * | ft name,mail,groupcategory,groupscope,description
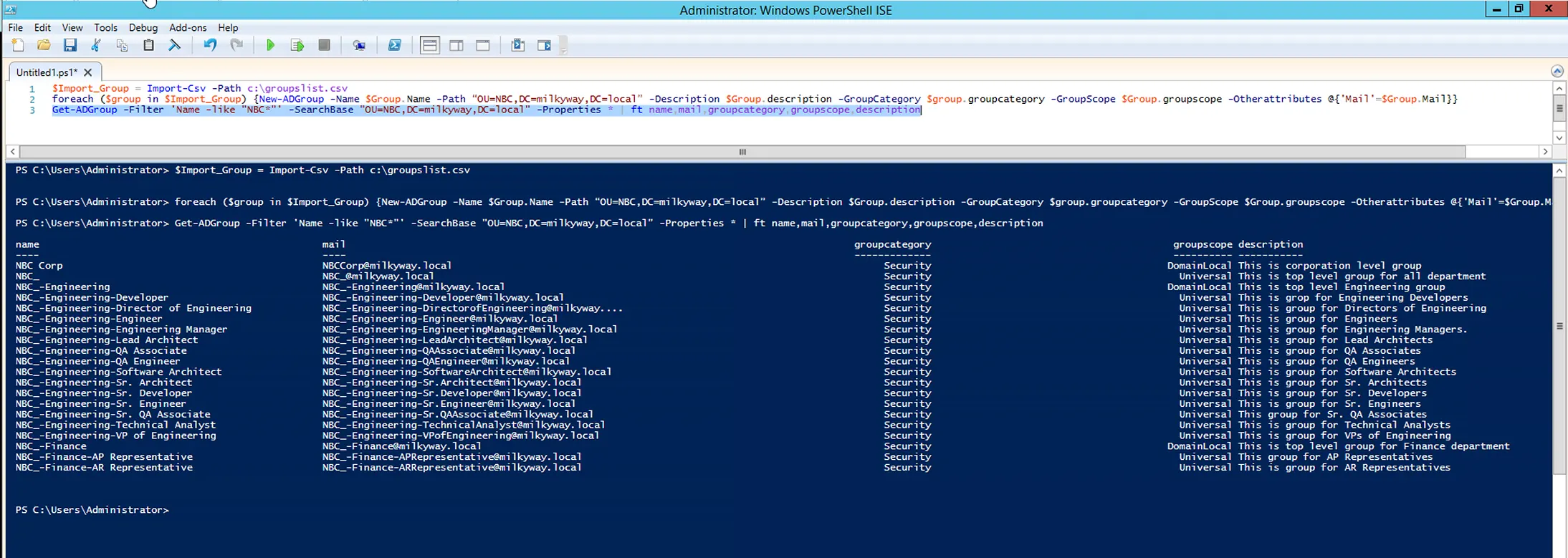
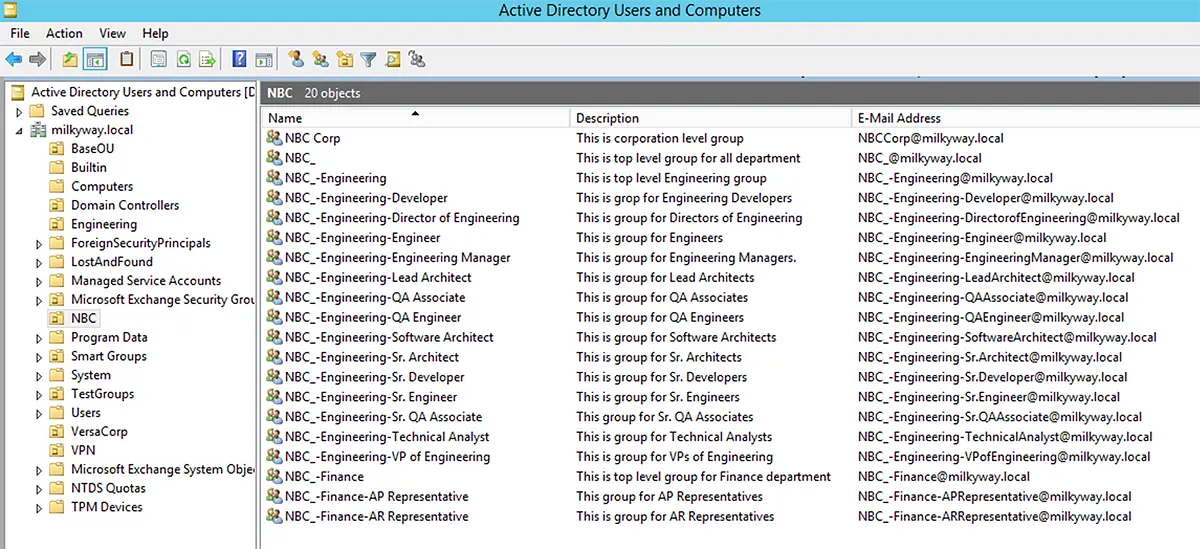
Below screenshot displays newly created groups in ADUC.
Create a Group with Other Attributes
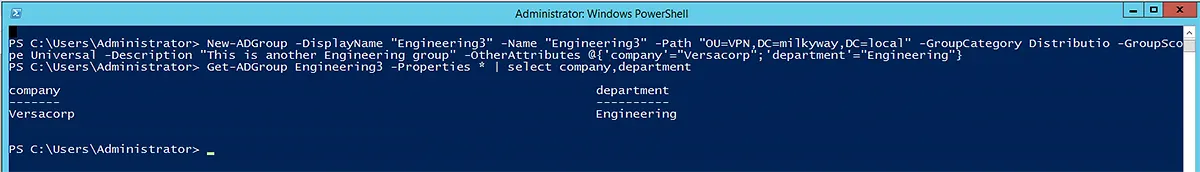
The New-ADGroup cmdlet has a handful of parameters to define the common group attributes, like group category, group scope, description, etc. However, you can use the -OtherAttributes parameter to populate any attribute of a group with values, as shown below:
New-ADGroup -DisplayName "Engineering3" -Name "Engineering3" -Path "OU=VPN,DC=milkyway,DC=local" -GroupCategory Distributio -GroupScope Universal -Description "This is another Engineering group" -OtherAttributes @{'company'=”Versacorp”;'department'=”Engineering”}
Create Groups with GroupID
GroupID is a powerful tool for creating smart groups in the directory. It can work with Active Directory and Azure AD to facilitate group creation and management.
You can use the following GroupID modules to create groups:
- GroupID Management Shell
- GroupID Automate
- GroupID Self-Service
GroupID Management Shell as an Alternative to PowerShell
GroupID Management Shell is a command-line interface that allows you to create and manage users, mailboxes, contacts, and groups in identity stores created for Active Directory and Azure. You can also create and manage dynamic groups.
The New-Group Cmdlet
Equivalent to the New-ADGroup cmdlet, GroupID Management Shell has the New-Group cmdlet that lets you create a new unmanaged/static group in a particular container in the directory.

Syntax
The New-Group cmdlet has the following syntax:
New-Group -SamAccountName -Name -OrganizationalUnit -GroupScope -Type -SecurityType [-GroupAlias ] [-ManagedBy <string[]>] [-DisplayName ] [-MailEnabled ] [-Description ] [-AdditionalOwners <string[]>] [-NotifyOptOutAdditionalOwners <string[]>] [-Members <string[]>] [-IdentityStoreId ] [-SecurityToken ] [-Credential ]
Required Parameters
The New-Group cmdlet requires the following parameters:
- SamAccountName
- Name
- OrganizationalUnit
- GroupScope
- Type
- SecurityType
GroupID Automate
Using GroupID Automate empowers IT to:
- Create static groups, smart groups and dynasties.
- Manage the type, scope, security type, and ownerships of groups.
- Manage group membership dynamically.
- Specify an expiry policy for groups. This policy defines the period for which the group remains active. When the period is over, the group becomes inactive and is locked in all activities.
- Move groups between domains within a single forest.
Examples of directory groups include security groups and distribution lists.
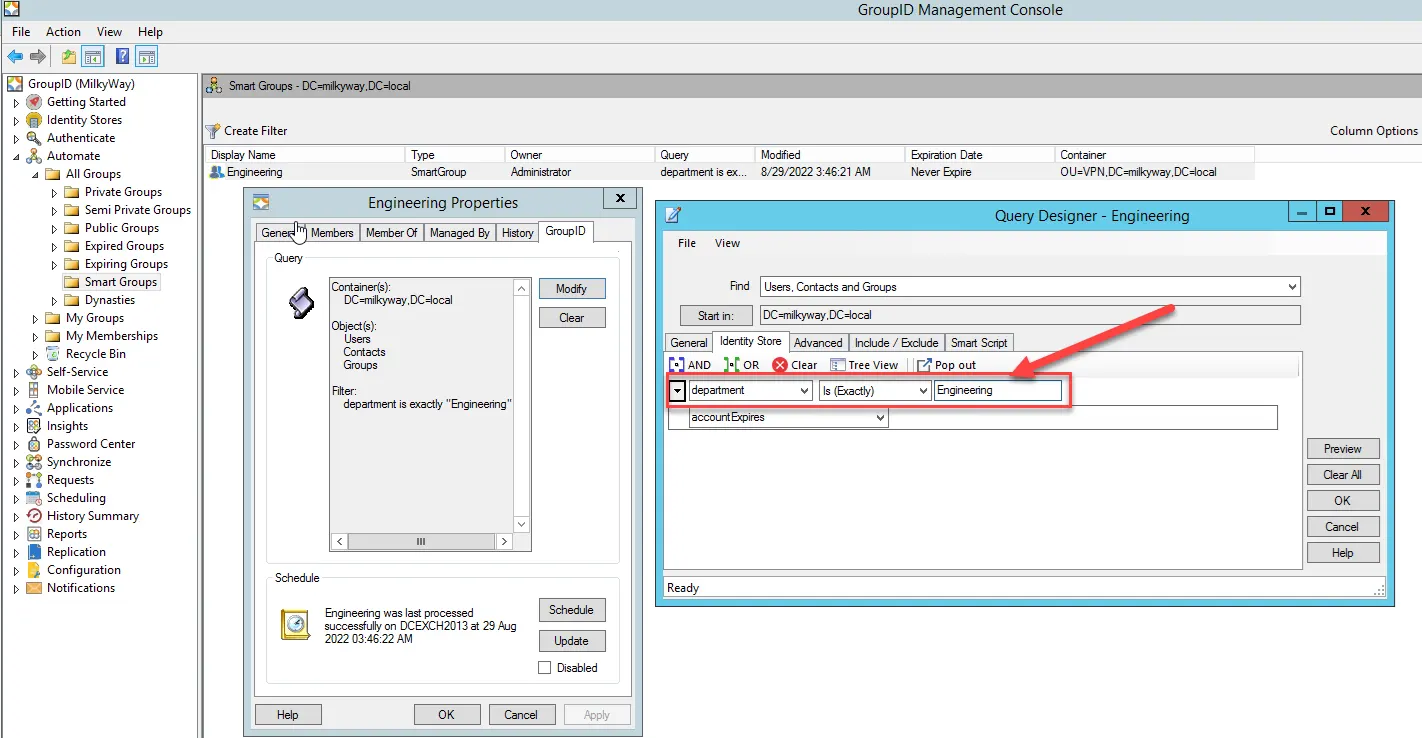
Automate empowers you to create smart groups in the directory. A smart group is a group whose membership is dynamically updated with a user-defined query.
- When you create a smart group, you associate an LDAP query with it.
- When this query is executed, it retrieves records from the directory and updates group membership.
The following screenshot shows an example of a user-defined query that would fetch all users whose department is set to Engineering and add them to the group’s membership. Automate also removes the users from the respective groups when their directory information changes, or they are deprovisioned.
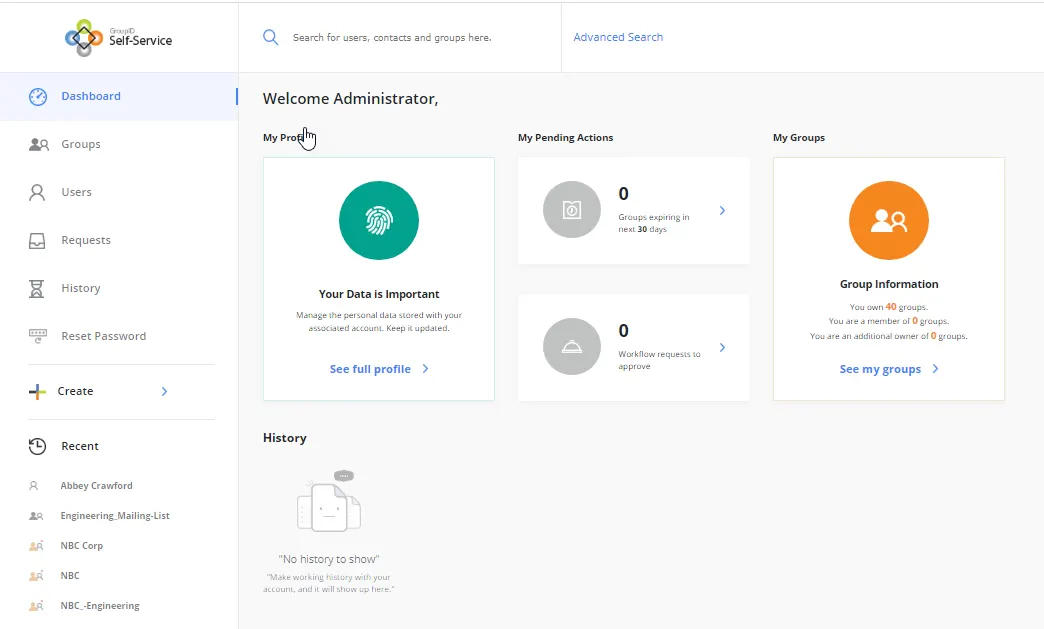
GroupID Self-Service
The GroupID Self-Service portal enables end-users to create and manage their groups in the directory. Users can:
- Search the directory
- Create and update directory objects
- Maintain and update their directory profiles
The following screenshot of the GroupID Self-Service portal shows the dashboard for the logged in user and a few useful links to navigate within the portal:
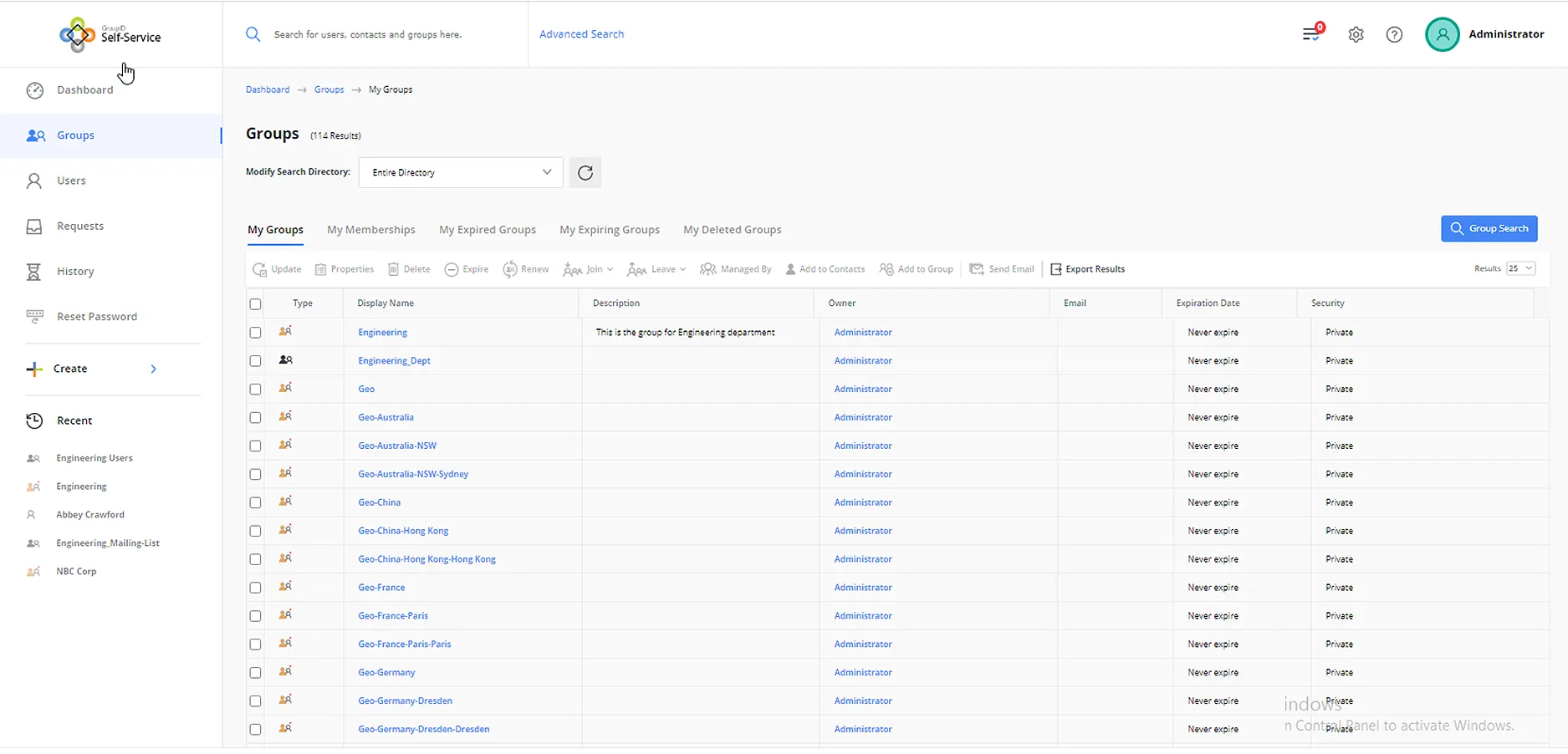
In the following screenshot, you can see the Groups page of the portal with different tabs, such as:
- My groups (lists the groups that the logged-on user owns)
- My membership (lists the groups the logged-on user is a member of)
- The other tabs relate to the powerful group expiration feature of GroupID
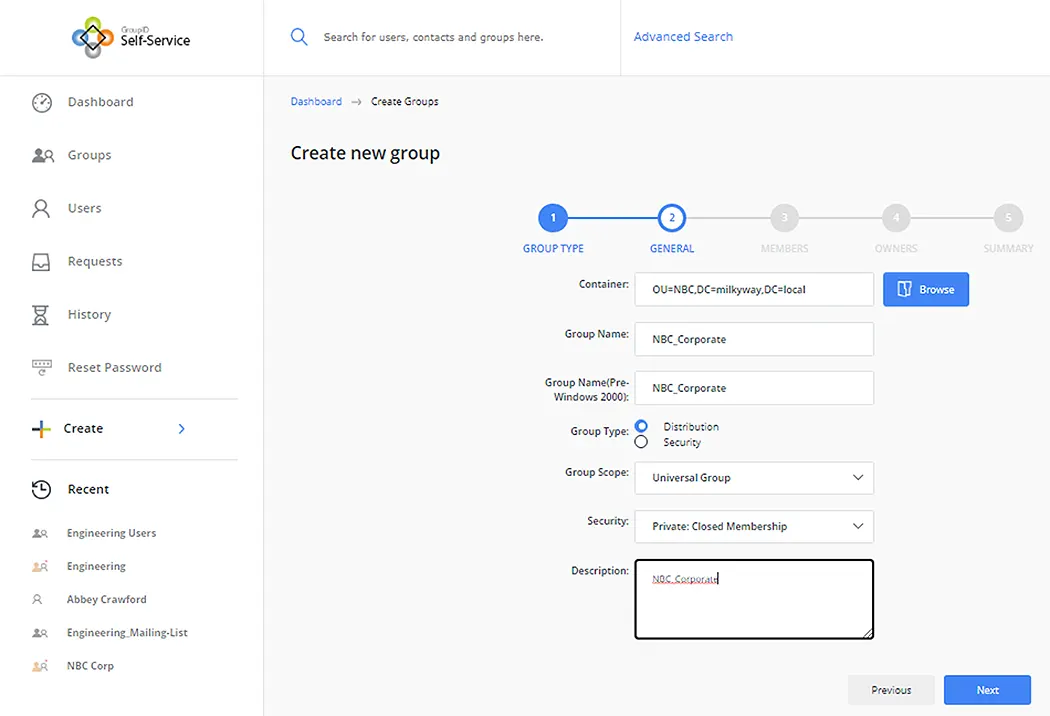
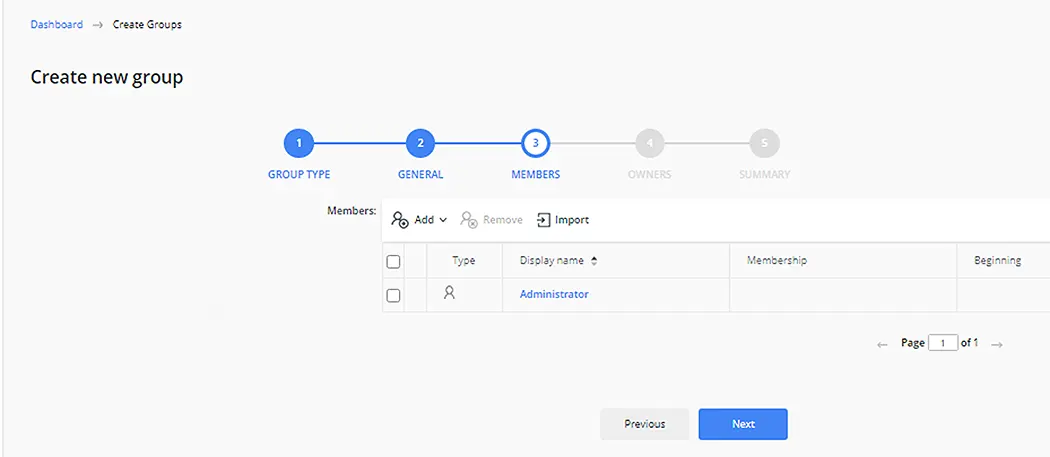
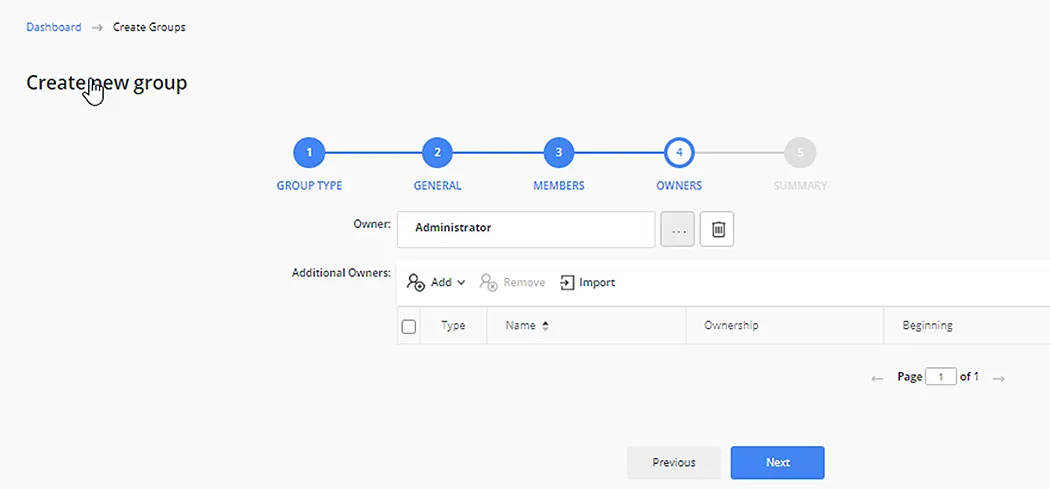
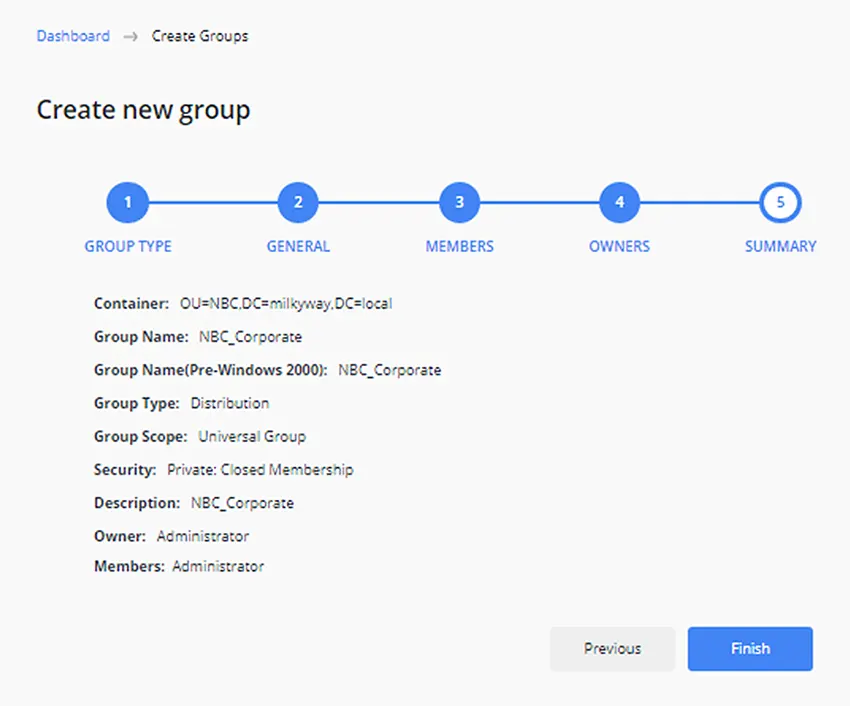
Create a Group using the Self-Service Portal
The process of creating a new group using the Create New Group wizard in the Self-Service portal is discussed below.
- Select the type of group you want to create, i.e., Static Group or Smart Group.
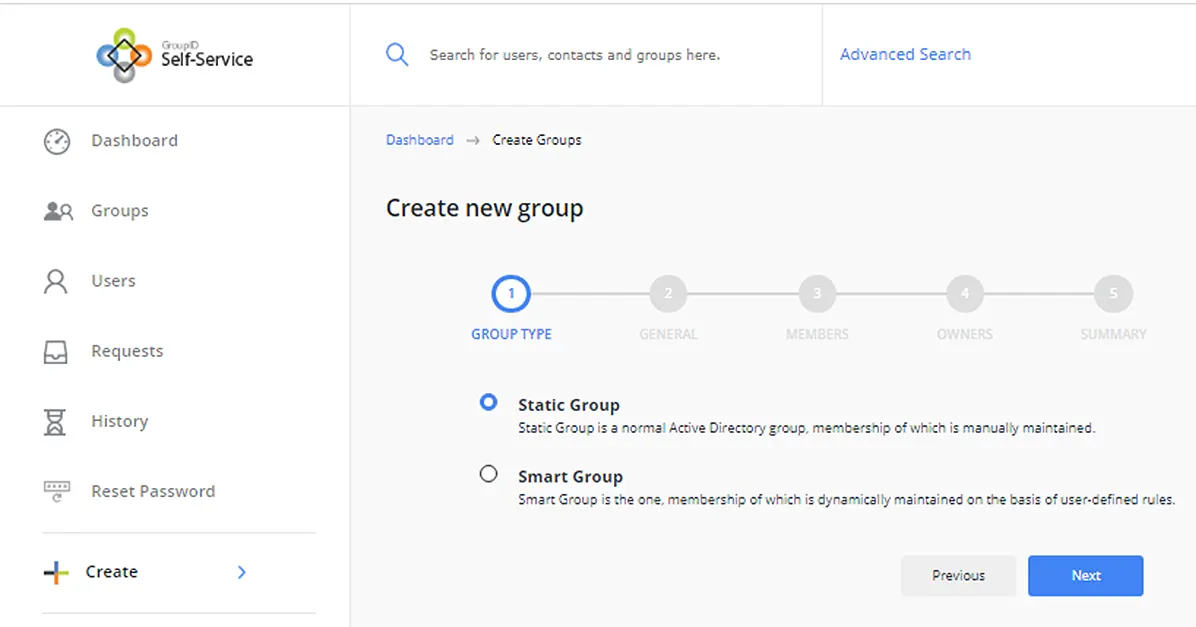
- Select the OU where group will be created. Also provide a Name, Group Type, Group Scope, and Description.
- On the following page, you can search and add members to the group.
- Next, specify a primary owner and additional owners for the group.
- On the last page of the wizard, review a summary of the group before creating it.
When end-users maintain and update their own groups, data is more accurate and reliable. Administrators can apply checks to control what users can view and change in the directory using the portal, for example:
- Role-based access helps delegate group creation to specific roles.
- Administrators can determine what attributes to expose for group creation and update.
- Workflows can be implemented to ensure that correct data is entered before applying changes in the directory.
- Notification emails are sent to designated recipients when a user makes any change to an object in the directory.
- History is tracked for all objects.
This makes Self-Service a secure tool to delegate group creation to end-users.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

