While authentication and authorization are often used interchangeably, both are considered as separate processes that are used to protect an organization from cyber-attacks. Authentication and authorization are significant parts of the first line of defense against data theft. As data breaches continue to increase in frequency and scale, strong authentication and authorization techniques should be a key component of every organization’s overall security strategy.
A user’s identity can be verified using a variety of authentication technologies before access is granted, such as passwords and fingerprints. Doing so adds a layer of protection and prevents security lapses like data breaches. Though, it is often the combination of distinct types of authentications that provides secure system reinforcement against threats, authentication and authorization work together to safeguard access to a resource. If you can’t prove your identity, you won’t be allowed into a resource.
Additionally, even if you can authenticate your identity, access will still be refused if you are not permitted to use that resource.
Table Of Contents
-
The Triple-A (AAA) Framework (Authentication, Authorization and Accounting)
-
What is Authentication?
-
How does Authentication Work?
-
Common Authentication Methods/Types
-
Password-based Authentication
-
Passwordless Authentication
-
Social Authentication
-
Single-Factor/Primary Authentication (SFA)
-
Two-Factor Authentication (2FA)
-
Three-Factor Authentication (3FA)
-
Single Sign-on (SSO)
-
Multifactor Authentication (MFA)
-
One-Time PIN
-
Biometrics
-
Barcode and QR Code Authentication
-
-
Common Authentication Protocols
-
Password Authentication Protocol (PAP)
-
Challenge Handshake Authentication Protocol (CHAP)
-
Extensible Authentication Protocol (EAP)
-
LDAP (Lightweight Directory Access Protocol)
-
SAML (Security Assertion Markup Language)
-
SCIM (System for Cross-domain Identity Management)
-
OAuth (Open Authentication)
-
OpenID
-
XACML (Extensible Access Control Markup Language)
-
RADIUS (Remote Authentication Dial-In User Service)
-
Kerberos
-
-
What is Authorization?
-
Common Authorization Methods
-
Authentication vs. Authorization
-
RBAC by GroupID
The Triple-A (AAA) Framework (Authentication, Authorization and Accounting)
If an administrator is remotely accessing a router or a device via an IP address, it is possible that an unauthorized can use the same IP address to gain access to that device. So, how we can prevent this scenario?
- Firstly, we must put authentication as a security measure.
- Moreover, the packets exchanged between the devices should be encrypted to prevent any person from capturing that sensitive information.
The AAA framework is used to add these layers of security.
What is AAA (Authentication, Authorization, Accounting) Framework?
A standard-based architecture called AAA (Authentication, Authorization, Accounting) is used to manage who is allowed to access network resources, what they are allowed to do, and record the actions taken while doing so.
We will focus on the core part of Authentication and Authorization in this blog and will leave accounting aside for now.
What is Authentication?
Authentication is the process of establishing a claim, such as the legitimacy of a computer system user to confirm a person’s or a device’s identity. At some point, it might require validating personal identity documents or verifying the authenticity of a website with a digital certificate.
In a software application, the authentication process begins prior to any code is allowed to execute before the permission and throttle checks take place. To verify a user’s identity, different systems could require different kinds of credentials. The credentials often take the form of a password, which is a secret known only to the individual and the system.
Based on authentication factors, authentication can be categorized as follows:
- Knowledge Factors: Something you know, such as a password or the answer to a security question. These are referred to as “knowledge factors”.
- Possession Factors: Something you have, that is, a physical object like a mobile phone or security token. These are referred to as “possession factors”.
- Inherence Factors: Something you are or do, for example, your biometrics or patterns of behavior. These are referred to as “inherence factors”.
How Authentication Works?
Identification and real authentication are two separate stages of the authentication process.
- The Identification phase provides a user identity to the security system. This identity is provided in the form of a user ID. The security system will search all the objects that it knows and find the specific one that the actual user is currently applying leading to user been identified.
- The fact that the user claims does not necessarily mean that the user is true. An actual user can be mapped to another abstract user object in the system, and therefore be granted rights and permissions to use the system. The user must give evidence to prove his or her identity to the system. Authentication is the process of verifying a user’s claimed identity using evidence they have provided. This evidence is referred to as a credential.
Common Authentication Types
There are several authentication types. Users are often assigned a user ID for identification purposes, and authentication takes place when the user enters credentials, such a password, that exactly matches their user ID.
Single Factor Authentication (SFA) vs. Multi-factor Authentication (MFA)
- Single-factor authentication is the procedure of requiring a user ID and password (SFA).
- In recent years, companies have strengthened authentication by asking for additional authentication factors, such as:
- A unique code that is provided to a user over a mobile device when a sign-on is attempted,or
- A biometric signature, like a facial scan or thumbprint.
This is known as two-factor authentication (2FA) or multifactor authentication (MFA).
Some common authentication types are as follows:
- Password-based Authentication
- Password less Authentication
- Social Authentication
- Single-Factor/Primary Authentication (SFA)
- 2 factor Authentication (2FA)
- Three-factor authentication
- Single Sign ON (SSO)
- Multifactor Authentication (MFA)
- One time PIN
- Biometrics
- Barcode and QR Code Authentication
Password-based Authentication
A user inputs a distinct ID and key that are then verified against credentials that are kept as part of the password authentication procedure.
Whether it be a social media site or an online banking application, you are required to create and input a password to access a personal account. By doing this, you participate in a password authentication system that protects your confidential data from being accessed by unauthorized individuals.
How Password-based Authentication Works:
When a user establishes a password, the system or website stores a copy of that credential in a secure password database, where the server may check it against any subsequent login attempts. It’s crucial that password-based authentication solutions guarantee top-notch security for those databases because all those passwords are kept in one place (which would be a field day for hackers).
Typically, passwords are stored in an encrypted fashion so that even if a hacker can access the database, the information would be useless to them.
Password Policy
A password policy is a set of rules and guidelines that suggest how the passwords should be managed and chosen. A directory server supports multiple password policies. The password policy can be configured to suit the security requirements of your organization.
Directory server instances are initially created using a default password policy.
Password Less Authentication
Password less authentication is a type of authentication that allows a user to access a computer system without having to enter a password or any other secret knowledge.
In most common implementations, users are asked to enter their public identifier (username, phone number, email address, etc.) and then complete the authentication process by providing secure proof of identity through a registered device or token.
How Password Less Authentication Works
Password less authentication methods typically rely on public-key cryptography infrastructure, where the private key is stored on the user’s device (PC, smartphone, or an external security token) and can only be accessed by providing a biometric signature or another authentication factor that is not knowledge based. During registration to the authenticating service, the public key is provided from the remote server, application, or website.
Social Authentication
Social login is a form of single sign-on using existing information from a social networking service (such as Facebook, Twitter, or Google) to sign into a third-party website instead of creating a new login account specifically for that website.
It intends to:
- Make login processes simpler for consumers.
- Give web developers access to a growing body of accurate demographic data.
How Social Authentication Works
Typically utilizing a plug-in or a widget, social login connects accounts from one or more social networking services to a website. By selecting the desired social networking service, the user simply uses his or her login for that service to sign on to the website. As a result:
- Users are relieved of the burden of remembering login information for several electronic commerce and other websites.
- Website owners gain access to demographic data provided by social networking services.
For those who do not prefer it or do not have an account with a compatible social networking service, many websites that allow social login also to provide more conventional online registration.
Single-Factor/Primary Authentication (SFA)
The simplest type of authentication mechanism is single-factor authentication. SFA enables online self-verification by matching one credential. The most popular example of a SFA would be a password (credential) to a username.
Pros of SFA
SFA is the most widely used authentication method. Due to its simplicity and low cost of implementation, SFA is frequently employed by default in systems
Cons of SFA
SFA is regarded as being less safe than MFA, particularly when the identification is a weak password.
Best Practice for Single Factor Authentication
Password security depends on the diligence of the system management or the user who starts the account. Following are the best practices pertaining to Single Factor Authentication (SFA):
- Generate a strong password.
- Ensure no one can access it.
Two-Factor Authentication (2FA)
Two-factor authentication, also known as multifactor authentication, is a type of electronic authentication in which a user is only granted access to a website or application after successfully providing two or more pieces of evidence, such as
- Knowledge (something only the user knows)
- Possession (something only the user has)
- Inherence (something only the user is)
Authentication factors include one-time password sent to a mobile device, phone number reputation scoring, subscriber status, and more.
Benefits of Two Factor Authentication
2FA prevents unauthorized third parties who may have figured out a single password from accessing user data containing personal identification or financial assets.
Two-factor authentication significantly decreases the risk of hackers accessing online accounts, blocking 96% of bulk phishing attacks. To achieve a secure & scalable product, it becomes essential that digital identity & 2FA are combined.
Three-Factor Authentication (3FA)
Three-factor authentication also comes under multifactor authentication (MFA) as it uses three distinct factors for authentication.
It involves three authentication mediums to verify a user’s identity before granting them access.
How Three-Factor Authentication (3FA) Works
With 3FA, administrators can adopt additional security measures while respecting the time and labor of employees. 3FA factors include:
- Mobile devices (push notifications for iOS and Android authenticator apps)
- Biometric (face and fingerprint scan)
- Voice recognition
- SMS codes
- One-time passwords
For a system to be termed three-factor authentication, at least one element from each of the above categories must be used; choosing three authentication elements from just two categories is considered two-factor authentication (2FA). Location can be used as a fourth element in four-factor authentication (4FA).
Benefits of 3FA
3FA dramatically improves security. This makes for a more secure log-in because it is improbable that an attacker could spoof or steal all three components used in 3FA. Most corporations and government organizations that demand high levels of security utilize three-factor authentication.
Single Sign-on (SSO)
SSO is an authentication method that enables users to sign into any number of connected but separate software systems using a single ID. With true single sign-on, a user only needs to log in once to access services without having to repeatedly provide their login details.
How Single Sign on Works
The term “single sign-on” describes systems where a single authentication grants access to numerous apps by smoothly transferring the authentication token to set up applications.
In contrast, single sign-off or single log-out (SLO) is a feature that allows access to numerous software systems to be terminated with a single sign-out action.
Example of Single-Sign On (SSO)
For example, if you log into a Google service such as Gmail, you are automatically authenticated to YouTube, AdSense, Google Analytics, and other Google apps. Likewise, if you log out of your Gmail or other Google apps, you are automatically logged out of all the apps; this is known as Single Logout.
Multifactor Authentication (MFA)
Multifactor authentication (MFA) is a security mechanism that confirms a user’s identity for a login or other transaction by requiring multiple ways of authentication from different categories of credentials.
MFA involves two or more independent credentials:
- What the user knows, such as a password.
- What the user has, such as a security token.
- What the user is, by using biometric verification methods.
A framework for identity and access management must include multifactor authentication as a fundamental element.
Pros of MFA
MFA aims to make it more challenging for an unauthorized person to access a target, such as a physical place, computing device, network, or database. The attacker must still overcome at least one or more barriers even if one is compromised or broken to get access to the target.
How MFA Works
MFA is used across verticals such as tech, banks shopping and more. Even if it goes by different names, like “Two-Step Verification” or “Multifactor Authentication,” the best ones all work on the same principles. When you sign into the account for the first time on a new device or app (like a web browser), you need more than just the username and password. To demonstrate who you are, you require a second item, or second “factor”.
One-Time PIN
A One-time password or pin (OTP), also known as one-time authorization code (OTAC), is a password or pin that is only valid for one login session or sometimes for one transaction, like in banks.
OTP and MFA
OTP is more refined authentication methods as compared to static password-based authentications methods. Several implementations also incorporate two-factor authentication by ensuring that the one-time password works with:
- Something a person has (such as a small keyring fob device with the OTP calculator built into it, or a smartcard or specific cellphone).
- Something a person knows (such as a PIN).
Pros of One-Time Pin
OTP generation algorithms typically make use of:
- Pseudo randomness or randomness to generate a shared key or seed, and Cryptographic hash functions, which can be used to derive a value but are hard to reverse, therefore making it difficult for an attacker to obtain data that was used for the hash. Otherwise, it would be simple to guess future OTPs by looking at past ones; therefore, cryptographic hash functions are required.
Biometrics
Biometrics are measurements of the body and computations of human traits. In computer science, access control and identity management are accomplished by biometric authentication, also known as realistic authentication.It is also used to locate people in groups that are being watched.
Examples include:
- Mouse movement
- Fingerprints
- Veins on the palms
- Face identification
- DNA
- Palm prints
- Hand geometry
- Iris recognition
- Retina
- Odor/Scent
Barcode and QR Code Authentication
Here’s how barcodes and QR codes are different:
- A barcode is an optical label that can be read by a computer and contains data about the object to which it is attached.
- QR codes frequently contain information for a tracker, location, or identifier that directs users to a website or application.
Barcode:
Using barcodes, data can be represented visually and in a way that is machine-readable. Specialized optical scanners known as barcode readers are used to read barcodes.
QR Code:
QR stands for “Quick Response Code.” QR code uses the following four defined encoding modes to store information efficiently:
- Alphanumeric
- Numeric
- Kanji
- Byte/binary
A camera or another imaging device can scan a QR code, which is made up of black squares organized in a square grid on a white background. Reed-Solomon error correction is then used to process the picture so that it can be properly decoded. Next, patterns found in the image’s horizontal and vertical components are used to extract the necessary data.
Common Authentication Protocols
Some common authentication protocols are:
- Password Authentication Protocol (PAP)
- Challenge Handshake Authentication Protocol (CHAP)
- Extensible Authentication Protocol (EAP)
- LDAP (Lightweight Directory Access Protocol)
- SAML (Security Assertion Markup Language)
- SCIM (System for Cross-domain Identity Management)
- OAuth
- OpenID
- XACML (Extensible Access Control Markup Language)
- RADIUS (Remote Authentication Dial-In User Service)
- Kerberos
Following is a discussion of these protocols.
Password Authentication Protocol (PAP)
Password Authentication Protocol (PAP) is a password-based authentication protocol used by Point-to-Point Protocol (PPP) to validate users.
It works as follows:
- PAP authentication requires the calling device to enter the username and password.
- If the credentials match either the remote AAA database or the local database of the calling device, access is permitted.
Challenge Handshake Authentication Protocol (CHAP)
The Point-to-Point Protocol (PPP) first employed the Challenge-Handshake Authentication Protocol (CHAP) in computing to authenticate users. PPP with CHAP is supported by most network access servers and all network operating systems. Other authentication protocols like RADIUS and Diameter also support CHAP.
Although the password is never broadcast over the network, CHAP requires that both the client and server know the clear-text version of it. When used in PPP, CHAP provides better security as compared to Password Authentication Protocol (PAP).
Extensible Authentication Protocol (EAP)
Extensible Authentication Protocol (EAP), which is often used in wireless networks and point-to-point connections, is an authentication framework rather than a particular authentication mechanism. It offers a few standard features and handles the negotiation of so-called EAP techniques for authentication.
Without needing to agree upon a certain authentication method beforehand, the EAP protocol can allow a variety of authentication methods. Approximately 40 alternative approaches have currently been defined.
LDAP (Lightweight Directory Access Protocol)
To manage and access directory information over an IP, an open-source protocol is employed known as LDAP (Lightweight Directory Access Protocol).
Directory services play a key role in developing intranet and internet applications by allowing the sharing of information about users, systems, networks, services, and applications throughout the network. Here are two examples:
- Using a corporate email directory as an example, directory services can offer any ordered collection of records with a hierarchical structure.
- Similarly, a telephone directory is a list of subscribers with an address and a phone number.
How LDAP Works
LDAP enables users to find information about entities, thus serving its core purpose.
- Information is stored in the LDAP directory and user authentication is required to access the directory.
- It also provides the communication language that applications require to send and receive information from directory services.
Read More: Difference Between LDAP and Active Directory
SAML (Security Assertion Markup Language)
An open standard for sharing authentication and authorization information, notably between identity providers and
Web-browser single sign-on is a significant use case that SAML addresses. Within a security domain, single sign-on is quite simple to implement (using cookies, for example), but extending SSO across security domains is more challenging and has led to the emergence of non-interoperable proprietary technologies. To encourage compatibility, the SAML Web Browser SSO profile was defined and standardized.
SCIM (System for Cross-domain Identity Management)
System for Cross-domain Identity Management is used for automating the sharing of user data between identity domains or IT systems.
Some examples of SCIM use are as follows:
-
User Record Management
SCIM can be used to add and remove individuals from an organization’s electronic employee directory as new employees are hired and separated from existing employees. In external systems like G Suite, Office 365, or Salesforce, SCIM might be used to automatically add/delete (or provision/deprovision) accounts for those users.
-
User Attribute Management
SCIM can also be used to share information about user attributes, attribute schema, and group membership. Attributes could range from user’s group membership or contact information. Group membership or other attribute values are used to manage user permissions.
Maintaining the pertinent data across many identity domains can be challenging because attribute values and group assignments are subject to change.
SCIM makes use of a standardized REST API with data that is represented in JSON or XML.
OAuth (Open Authentication)
OAuth is an open standard for access delegation. It is often used by online users to grant applications or websites access to their information on other websites without disclosing their passwords.
OAuth mechanism is used by companies such as Amazon, Google, Facebook, Microsoft, and Twitter to permit the users to share information about their accounts with third-party applications or websites.
OAuth employs permission tokens rather than sharing password information to establish an identity between customers and service providers. With the help of the OAuth authentication protocol, you can authorize an application to interact with another on your behalf without disclosing your password.
OpenID
The nonprofit OpenID Foundation promotes OpenID, an open standard and decentralized authentication mechanism.
OpenID enables users to log into multiple unrelated websites without needing a unique identity and password for each one. Users are authenticated by cooperating sites (referred to as relying parties or RP) using a third-party identity provider (IDP) service. This eliminates the need for webmasters to provide their own ad hoc login systems. Users create accounts by choosing an OpenID identity provider, and then login into any website that supports OpenID authentication using those accounts.
XACML (Extensible Access Control Markup Language)
The XACML standard establishes an architecture, a processing model, and a declarative fine-grained, attribute-based access control policy language that describe how to analyze access requests according to the rules set out in policies.
One of the objectives of XACML as a published standard specification is to encourage consistent nomenclature and compatibility between access control implementations by various suppliers. To determine whether a given user is permitted to access a certain resource in a particular way, XACML relies on attribute-based access control system (ABAC). ABAC is also referred to as PBAC where “P” implies “Policy” for policy-based access control. As a subset of ABAC, role-based access control (RBAC) can also be used with XACML.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol called Remote Authentication Dial-In User Service (RADIUS) offers centralized authentication, authorization, and accounting (AAA) administration for users who connect to and use a network service.
Using either TCP or UDP, RADIUS is a client/server protocol that runs in the application layer. The RADIUS client component of network access servers, which manage network access, typically talks with the RADIUS server. RADIUS server runs in the background on UNIX or Windows.
Kerberos
A computer network authentication technique called Kerberos uses tickets to enable nodes communicate over an insecure network to securely verify each other’s identities.
It offers mutual authentication, whereby the user and the server independently confirm each other’s identities. A trusted third party is necessary for Kerberos, which draws on symmetric-key cryptography. Optionally, public-key cryptography may be used at points in the authentication process.
Kerberos protocol is inspired by the fierce three-headed guard dog of Hades from Greek mythology (also known as Cerberus).
What is Authorization?
While authentication is the process of verifying that “you are who you say you are”, authorization is the process of verifying that “you are permitted to do what you are trying to do”.
When authorization and authentication subsequently happen, it doesn’t imply that after authentication, authorization is required. It is possible for an anonymous agent to be authorized.
Access control, general information security, computer security, and the role of specifying access rights and privileges to resources are all related to authorization. Generally speaking, “to authorize” means to set an access policy. For instance, access to employee records is often granted for human resources workers.
In authorization, the system employs the access control rules to determine whether to approve (grant) or deny (rejected) access requests from (authenticated) users. Resources include individual files or an item’s data, computer programs, computer devices, and functionality provided by computer applications. Computer users, software, and other computer hardware are examples of customers.
Anonymous or guest users are not required to authenticate. They often have limited access and permissions.
Common Authorization Methods
Following are some common authorization protocols:
- Mandatory Access Control (MAC)
- Role-Based Access Control (RBAC)
- Attribute-Based Access Control (ABAC)
- Discretionary Access Control (DAC)
Here is a discussion of these protocols.
Mandatory Access Control (MAC)
Mandatory access control (MAC) is a type of access control used in computer security where the operating system or database limits a subject’s or initiator’s ability to access or otherwise interact with a target.
- In operating systems, a subject is typically a process or thread.
- Objects refers to files, directories, shared memory segments, TCP/UDP ports, IO devices, etc.
Each subject and object have a unique collection of security characteristics. An authorization rule imposed by the operating system kernel evaluates these security properties whenever a subject tries to access an object and determines whether the access is permitted or not. Any action taken by any subject on any object is evaluated to see if it complies with the authorization rules (also known as the policy).
Mandatory access control is another option available in the access control mechanism of a database management system. In this case, the objects are tables, views, procedures, etc.
With required access control, the administrator centrally manages this security policy and users are unable to override it. Contrarily, discretionary access control (DAC), which likewise regulates subjects’ access to objects, gives users the power to set security parameters and/or decide on policy. (The traditional Unix system of users, groups, and read-write-execute permissions is an example of DAC.).
Systems with MAC capabilities enable policy administrators to put organization-wide security rules into action. Users cannot mistakenly or purposefully override or modify this policy (unlike DAC) enabling the admins to define a central policy and enforcing it across users.
Role-Based Access Control (RBAC)
Role-based access control (RBAC), often known as role-based security, is a method for limiting system access to authorized users in computer system security. Moreover, it is also referred to as the strategy of implementing one of the following:
- Mandatory Access Control (MAC)
- Discretionary Access Control (DAC).
RBAC is a policy-neutral access-control technique built around roles and privileges. User assignments are made simple by RBAC’s components, such as role-permissions, user to role, and role to role linkages.
RBAC can be used to simplify security administration in large businesses with thousands of permissions and hundreds of users. Even though RBAC is distinct from MAC and DAC access control frameworks, it may easily enforce these restrictions. For instance, if you were using RBAC to manage user access to an HR application, you could grant HR managers permission to edit employee information while restricting other staff members’ access to view only their own information.
Attribute-based Access Control (ABAC)
The term “attribute-based access control” (ABAC) refers to a model of access control where users are given access rights based on policies that integrate many attributes.
The policies may make use of any properties (user attributes, resource attributes, object, environment attributes, etc.). This model supports Boolean logic, in which rules contain “IF, THEN” statements about who is making the request, the resource, and the action. For example, if the requester is a manager, then grant read/write access to confidential data.
The NIST framework introduces the main concepts of ABAC as its operations, such as:
- Policy Administration Point (PAP)
- Policy Enforcement Point (PEP)
- Policy Decision Point (PDP)
- Policy Information Point (PIP).
The key distinction between ABAC and RBAC is the idea of policies.
| ABAC expresses a complex Boolean rule set that can evaluate many different attributes. | RBAC uses predefined roles with a specific set of privileges associated with them and to which subjects are assigned. |
Microsoft sometimes defines ABAC as policy-based access control (PBAC) or claims-based access control (CBAC).
Discretionary Access Control (DAC)
DAC refers to an access control policy being implemented over all objects in an information system. Moreover, purpose of the policy is to enable the objects to do one of the following:
- Pass the information to other subjects or objects.
- Allow its privileges to other subjects.
- Alter the security attributes on objects, subjects, system components, or information systems.
- Select the security attributes to be applied to newly created or updated objects.
- Alter the rules of access control.
The policies are optional in the sense that a subject with distinct access permissions can provide those permissions on to any other subject.
Mandatory access control frequently goes against discretionary access control (MAC). On occasions, when a system lacks the required access control, it is considered to have “discretionary” or “purely discretionary” access control.
- DAC refers to the first category of access controls that subjects can transfer among one another.
- MAC refers to a second category of access controls that places restrictions on the first.
Systems can implement both MAC and DAC at the same time.
Authentication vs. Authorization
Despite the authentication and authorization sounding similar, the login process has two distinct phases. Understanding the difference between the two is key to successfully implementing an IAM (Identity and Access Management) solution.
Let’s use an analogy to outline the differences. Consider a person walking up to a locked door to provide care to a pet while the family is away on vacation. That person needs:
- Authentication, as the form of a key. The lock on the door only grants access to someone with the proper key. Similarly, a system only grants access to users who have the right credentials.
- Authorization, as the form of permissions. Once inside the room, the person has the authorization to use the kitchen and open the cupboard that holds the pet food. The person does not have the permission to go in the bedroom.
Authentication and authorization work together in this example. After being authenticated, a pet sitter has permission to enter the place and access some areas (authorization).
IAM administrators need to be aware of the fundamentals of using authentication and authorization, as well as how they differ from one another. Organizations should be protected by implementing authentication with the appropriate authorization procedures.
Differences between Authentication vs Authorization
The following table lists the differences between authentication and authorization.
| Authentication | Authorization |
|---|---|
| Authentication verifies who the user is. | Authorization determines what resources a user can access. |
| Authentication works via passwords, biometric information, one-time PINS, and other information provided or entered by the user. | Authorization works via settings that are maintained and implemented by the organization. |
| Authentication comes first in a good identity and access management process. | Authorization always takes place after authentication. |
| The user may see authentication and make some changes to it. | The user is not able to see or alter authorization |
| Generally, transmits info through an ID Token. | Generally, transmits info through an Access Token. |
| Generally governed by the OpenID Connect (OIDC) protocol. | Generally governed by the OAuth 2.0 framework. |
| Under authentication, client and server are verified. | Under authorization, the defined policies and rules are used to verify if the user is allowed. |
| Authentication uses the popular authentication techniques, e.g., Password-based authentication, Password-less authentication, 2FA/MFA, Biometrics, SSO, and social authentication. | Authorization uses popular techniques like RBAC, ABAC, MAC, DAC, etc. |
| Technologies like JWT, SAML, OpenID Authorization, and OAuth are used in both authentication and authorization. | Technologies like JWT, SAML, OpenID Authorization, and OAuth are used in both authentication and authorization. |
| Example: By verifying their identity, employees can gain access to an HR application that includes their personal pay information, vacation time, and 401K data. | Example: Once the level of access has been allowed, employees and HR managers can access different levels of data depending on the permissions provided by the company. |
Role-based Access Control via GroupID
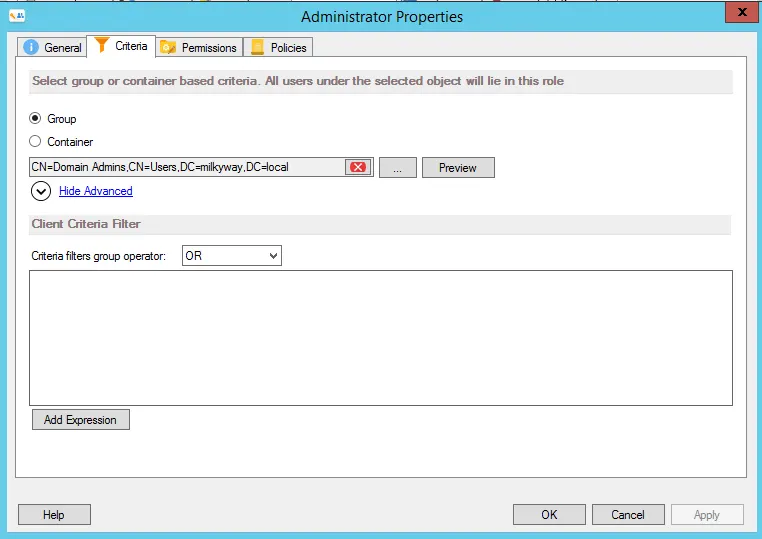
The actions that a user can perform in GroupID are based on their job function or role. An Active Directory identity store in GroupID has three predefined security roles:
- Administrator: By default, this role has permissions on all GroupID functions that can be performed within an identity store.
- Helpdesk: This role is available for the Password Center Helpdesk portal. Helpdesk users can update directory information for other users. They can also reset identity store account passwords and unlock identity store accounts on behalf of other users.
- User: role is assigned to regular users which enables them to create new groups, manage their groups, manage their directory profiles, and manage their identity store passwords.

These roles are highly customizable. You can modify their display name, priority level, permissions, policies, and more. You can also create more roles.
Creating a New Role
To define a role for an identity store in GroupID, you must specify the following
-
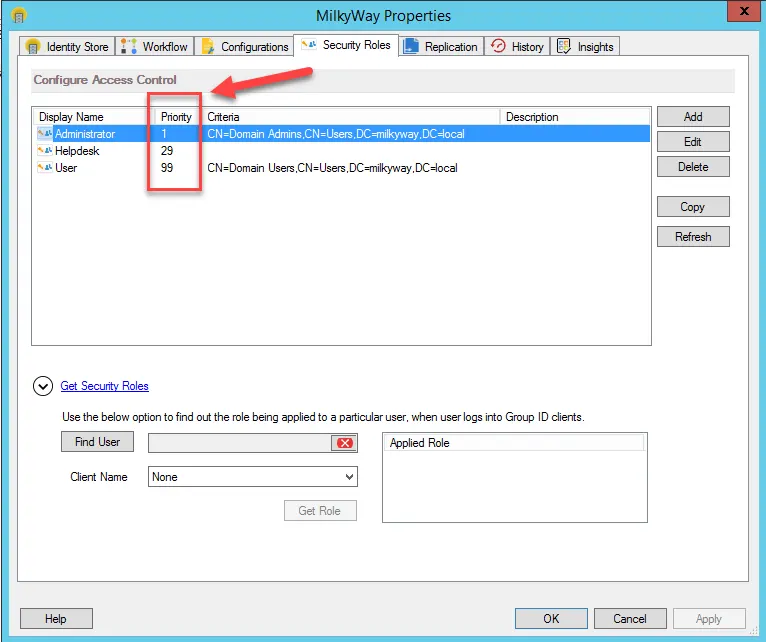
Criteria
Role criteria determines the users to whom the role applies. You can specify a group or a container as criteria, where group members or users residing in the specified containers would be assigned the role
-
Priority
Each role is assigned a value from 1-99, where 1 indicates the highest priority and 99 indicates the lowest priority. Role priority is unique for each role in an identity store.
Role priority is used for resolving conflicts when a user has more than one role. For example, when a user has two roles, Administrator and User, with role priority set to 1 and 25 respectively, then permissions and policies for the higher priority role (i.e., Administrator), would apply when the user logs into GroupID
-
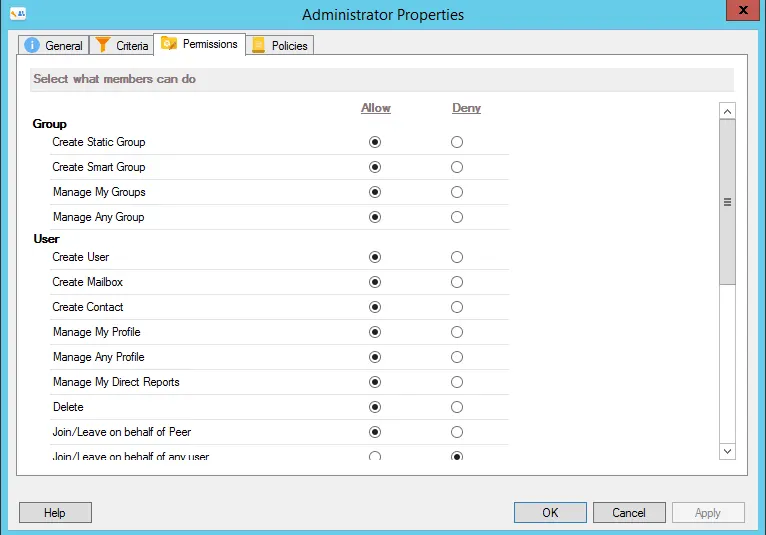
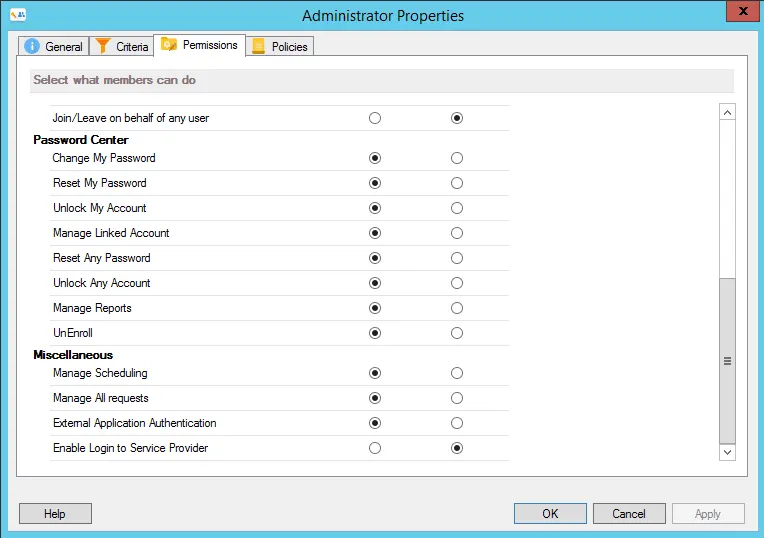
Permissions
Permissions refer to the different actions that role members can perform using GroupID, for example, creating directory objects, managing groups, managing scheduled jobs, managing user profiles, and more.
-
Policies
Policies refer to configurations that apply to role members. For example, the search policy can be applied to limit role members to search for objects only in a particular container.


Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

