Adding or removing users from Active Directory groups is a routine task for system administrators, but when it comes to large organizations, it is a time-consuming task if you do it manually. By ‘manual’, I mean using ADUC (Active Directory Users and Computers) or ADAC (Active Directory Administrative Center). However, the fact is:
- It’s perfectly okay to use ADUC or ADAC when one or two users have to be added.
- But when there is a need to add bulk users in groups, then PowerShell seems to be the best way to go.
The PowerShell cmdlet, Add-ADGroupMember, can easily add users, service accounts, computers, and groups as members in Active Directory groups.
Table Of Contents
-
Add-ADGroupMember Definition
-
Add-ADGroupMember – Syntax
-
Add-ADGroupMember – Parameters
-
Add a User to an AD Group using Add-ADGroupMember
-
Add Bulk Users to an AD Group using Add-ADGroupMember
-
Copy Group Members to Another Group
-
Add All Users from a Specific OU
-
Add Users Based on an AD Property
-
Add Users to a Group using a CSV File
-
Add Users to Different Groups using a CSV File
-
Managing Group Memberships with Imanami GroupID
-
Summary
Add-ADGroupMember Definition
“The Add-ADGroupMember command can be used to add one or more users, service accounts, computers, or groups as member of an Active Directory group.”
- The core parameter of this cmdlet is the Identity parameter, which specifies the Active Directory group that you want to add the new members to. You can also use:
- DN (Distinguished Name)
- GUID (Globally Unique Identifier)
- SAM (Security Accounts Manager) name of the group to identify it.
- You can also use the group identity as a variable to be used later in the cmdlet.
- You can also pass the group object to this command through the pipeline. For instance, run the Get-ADGroup command to get the group object using the identity parameter and then pass the object via pipeline to the Add-ADGroupMember cmdlet to process the membership.
Moreover,
- Another key parameter is the Members parameter, which specifies the new members being added to a group. You can identify the member by its distinguished name, security identifier, GUID or SAM Account name.
- Same as group identity, members can also be stored in a variable, to be used later in the cmdlet. You can use multiple members using the comma as a separator.
- User, group, and computer objects cannot be passed through pipeline using the Add-ADGroupMember. You can, however, use the Add-ADPrincipalGroupMembership command to add user, computer and group objects by using the pipeline.
Add-ADGroupMember – Syntax
The syntax of the Add-ADGroupMember cmdlet is as follows:
Add-ADGroupMember [-WhatIf] [-Confirm] [-AuthType ] [-Credential ] [-Identity] [-Members] <ADPrincipal[]> [-MemberTimeToLive ] [-Partition ] [-PassThru] [-Server ] [-DisablePermissiveModify]
Add-ADGroupMember – Parameters
The Add-ADGroupMember cmdlet uses the following parameters.
| Parameter | Description |
|---|---|
| -WhatIf | This parameter is used to see what the cmdlet is supposed to do. |
| -Confirm | If you want a confirmation prompt before running the command, you can use this parameter. |
| -AuthType | Used to select the authentication type: Basic or Negotiate. |
| -Credential | Can be used to provide alternative credentials. |
| -Identity | It is the most important attribute. Used to select the object on which the command will perform the actions. |
| -Members | This parameter is used to add members to the group selected in the Identity parameter. |
| -MemberTimeToLive | Used to provide a specific timeframe for the user to remain a member of the group. |
| -Partition | Used to specify the Active Directory partition. It accepts distinguished name as value. |
| -PassThru | Returns the object that is modified. |
| -Server | Use this parameter to specify the Active Directory instance you are connecting with. It takes the fully qualified domain name or simply the domain name, either with port or without port, as value. |
| -DisablePermissiveModify | Used to prevent the cmdlet from throwing an error if the user is already a member of the group. |
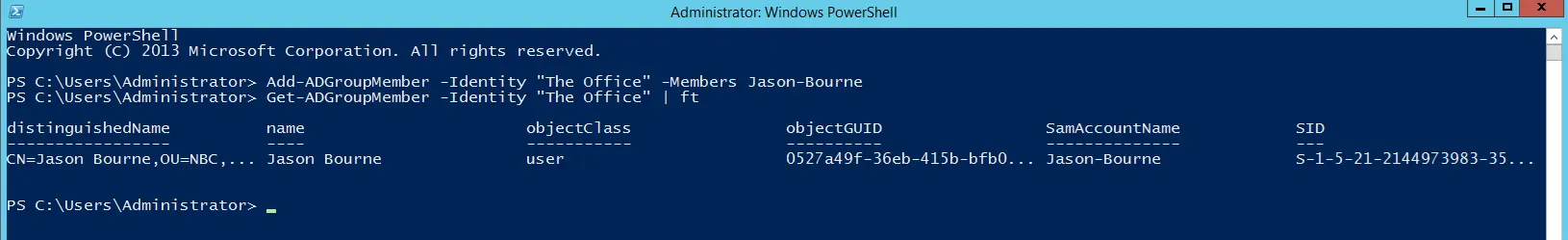
Add a User to an AD Group using Add-ADGroupMember
In this scenario, we will add “Jason-Bourne” to the group, “The Office”, using the following cmdlet:
Add-ADGroupMember -Identity "The Office" -Members Jason-Bourne
The above command will not show any output in the PowerShell console, so we will use the following command to check the membership of the group.
Get-ADGroupMember -Identity "The Office" | ft
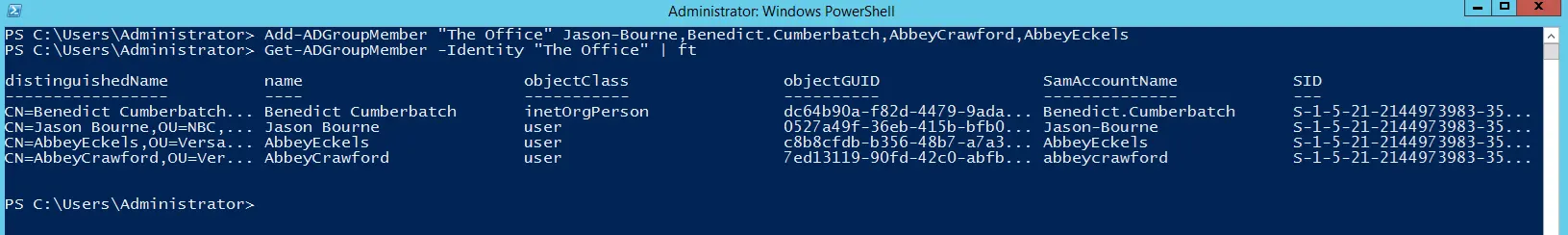
Add Bulk Users to an AD Group using Add-ADGroupMember
You can also add multiple users to a group by separating them with a comma, as shown below.
Add-ADGroupMember "The Office" Jason-Bourne,Benedict.Cumberbatch,AbbeyCrawford,AbbeyEckels
Let’s confirm the results by using the following command (where “The Office” is the group name).
Get-ADGroupMember -Identity "The Office" | ft
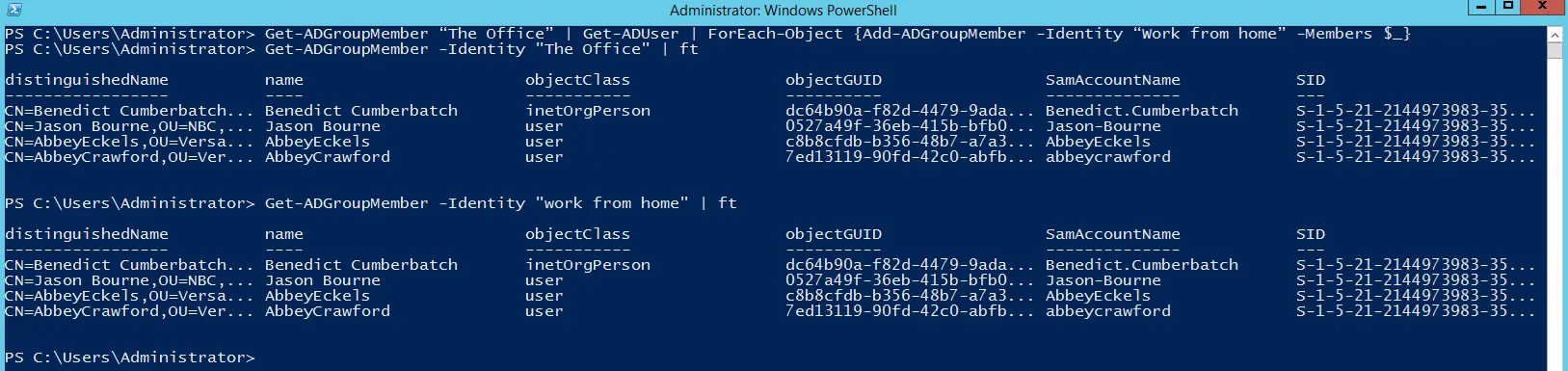
Copy Group Members to Another Group
Let’s assume you want to get a list of members from one group and add them to another group. We can do that by using the Get-ADGroupMember cmdlet, then pass the output through pipeline and a For loop, and finally add them to the second group using the Add-ADGroupMember command.
Get-ADGroupMember “The Office” | Get-ADUser | ForEach-Object {Add-ADGroupMember -Identity “Work from home” -Members $_}
The above command will perform the operation but will not show any output. Let’s use the following two commands to view the membership details of both groups.
Get-ADGroupMember -Identity "The Office" | ft Get-ADGroupMember -Identity "Work from home" | ft
Add All Users from a Specific OU
Now you have a requirement where you have created a group for an engineering project and you want to add all the users in the Engineering department to that group.
You can do so by searching all the users in the Engineering OU, as shown below. Notice that we have an OU named Engineering, and by looking at the Job Title and Department columns, it’s evident that all users belong to the Engineering department.

In the following command, we have used Get-ADUser that searches in the Engineering OU, then we have used a loop for each user object, and finally we have used the Add-ADGroupMember command to add those users to the Engineering Users group.
Get-ADUser -Filter * -SearchBase “OU=Engineering,DC=milkyway,DC=local”| ForEach-Object -process {Add-ADGroupMember -identity "Engineering Users" -Members $_.SamAccountName}
Let’s get the membership of the Engineering Users group by using the following command.
Get-ADGroupMember -Identity "Engineering Users" | ft

Add Users Based on an AD Property
Users can be selected and then added to a group depending on the value of an AD property. Run the following command, for instance, to filters users whose department attribute is set to Engineering, and then add them to the Engineering Users group.
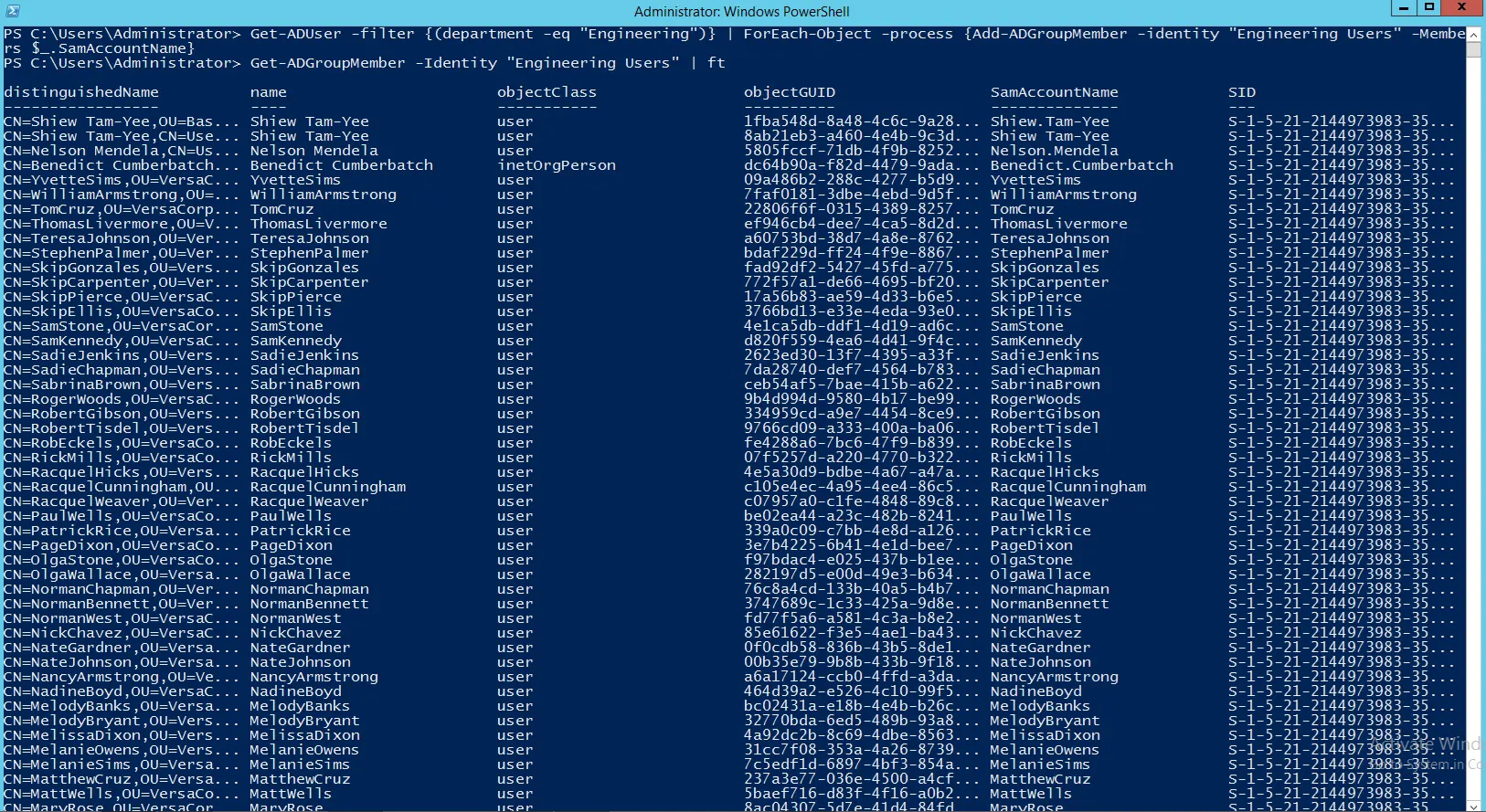
Get-ADUser -filter {(department -eq "Engineering")} | ForEach-Object -process {Add-ADGroupMember -identity "Engineering Users" -Members $_.SamAccountName}
Let’s confirm the changes by running the following command.
Get-ADGroupMember -Identity "Engineering Users" | ft
Add Users to a Group using a CSV File
It may happen that HR shares a CSV file with a list of users’ SAM (Security Accounts Manager) Account Names and asks you to add them to a specific group.
In this case, you can use the file in a PowerShell script with the Add-ADGroupMember cmdlet, that will add the users to the respective group using a For loop for each user.
The following screenshot shows a CSV file with the users’ SAM Account Names. It is opened with Excel for a better view of the columns. I have shown other columns too, which may be referenced later in this blog.

Below is the actual comma delimited file shown in notepad. For this example, we will use the “Name” column to add the users to a certain group.
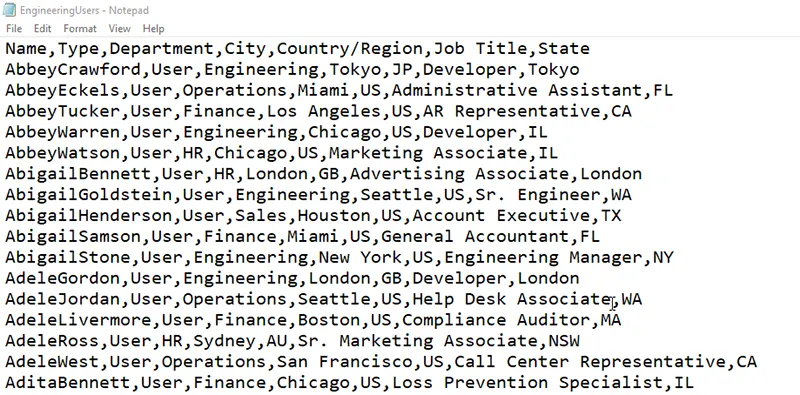
Using the following cmdlet, we will use the “Name” column in the CSV file to add all the users to the Engineering Users group.
Import-Csv -Path C:\engineeringusers.csv | foreach-object {Add-ADGroupMember -Identity "Engineering Users" -Members $_.Name}
Let’s verify the action by running the Get command.
Get-ADGroupMember -Identity "Engineering Users" | ft

Add Users to Different Groups using a CSV File
Now consider another scenario where you need to add specific users to specific groups and you have a CSV file containing usernames along with the group names where they should be added as members. It is as shown below.
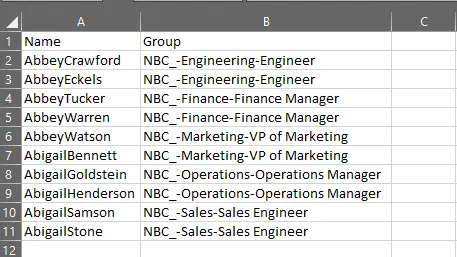
We will use the following cmdlet to add members to 5 different groups mentioned in the Group column of the CSV file, and will use the Name column to pick the users.
Import-Csv -Path C:\UsersAndGroups.csv | foreach-object {Add-ADGroupMember -Identity $_.Group -Members $_.Name}
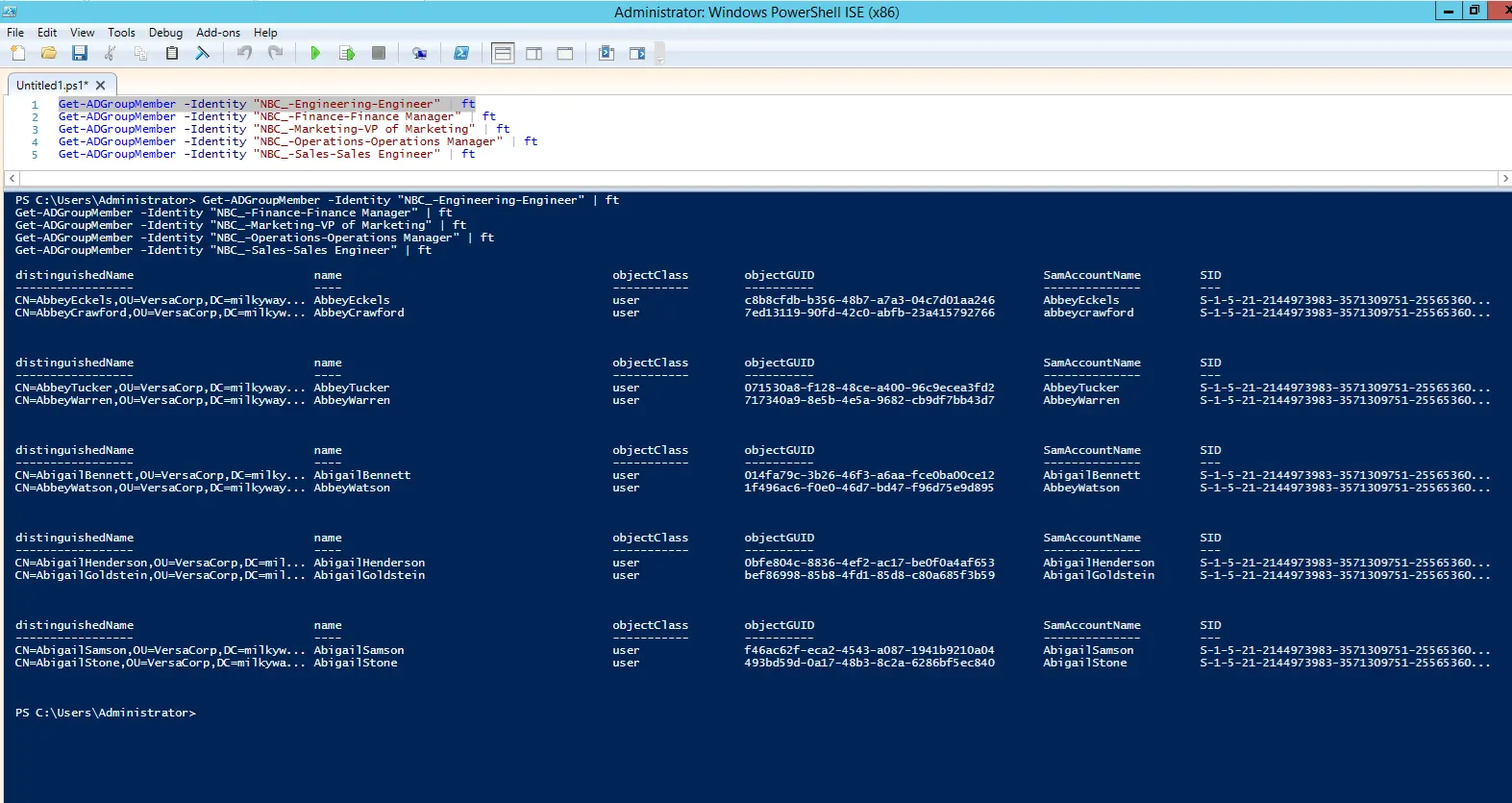
Obviously, the Add-ADGroupMember command does not produce any output. We can use the Get-ADGroup Member along with 5 different group names mentioned in CSV file to view their memberships:
We will use the Get-ADGroupMember command with the 5 different group names mentioned in the CSV file to view their memberships. Group names are as follows:
- Engineering-Engineer
- Finance-Finance Manager
- Marketing-VP of Marketing
- Operations-Operations Manager
- Sales-Sales Engineer
Managing Group Memberships with Imanami GroupID
When it comes to adding multiple members to a group or multiple members to multiple groups, experienced administrators feel the need to automate this process. It is here that they need a third-party tool.
To atomate group memberships and empower end-users to manage the groups they own, Imanami GroupID offers the following tools:
- GroupID Automate
- GroupID Self-Service
- GroupID Management Shell
Automate Group Memberships with Query-based Smart Groups
GroupID Automate enables the administrator to do the following:
- Create Static Groups, Smart Groups and Dynasties.
- Manage The Type, Scope, Security Type, And Ownerships of Groups.
- Manage Group Membership Dynamically.
- Specify An Expiry Policy for Groups. This Policy Defines the Period for Which the Group Remains Active. When The Period Is Over, The Group Becomes Inactive and Is Locked In All Activities.
- Move Group Between Domains Within a Single Forest.
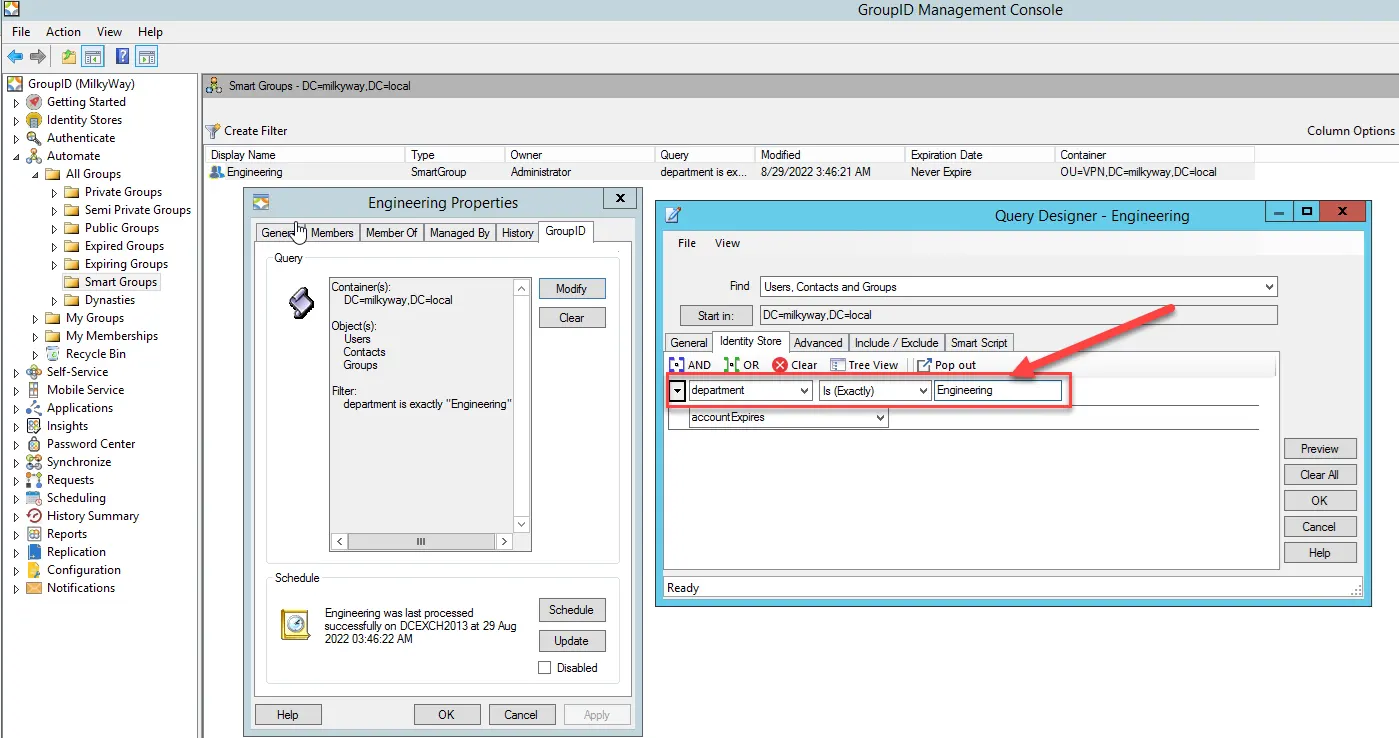
Here is how group memberships are determined in Automate:
- You can associate an LDAP query with a group.
- When this query runs, it retrieves records from the directory and adds them to group membership.
- You can schedule the query to run at a certain frequency for auto membership updates.
Hence, when user attributes change, Automate updates the relevant groups automatically. Automate also removes users from the respective groups when their attributes change or when they are deprovisioned, thus ensuring that groups are never out of date. This allows administrators to easily maintain large groups without having to manually add and remove members.
The following screenshot shows an example of a user-defined query that would fetch all users whose department is set to Engineering, and add them to the group’s membership.
Manage Group Memberships with AD Self-Service Web-Portal
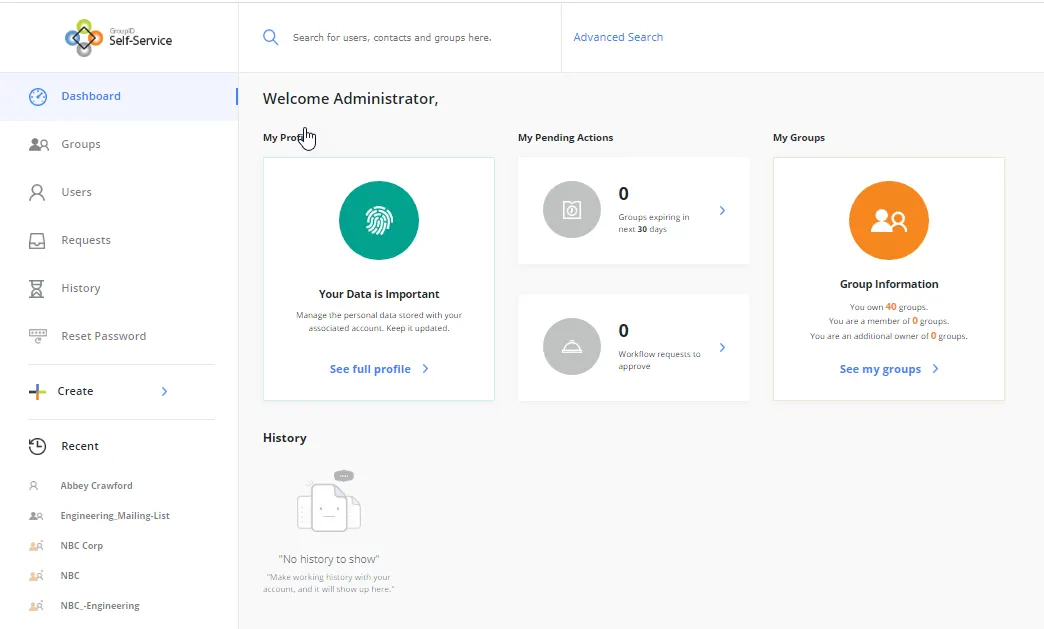
GroupID Self-Service is an active directory self service web portal that enables administrators to build and deploy web-based portals for end-users to carry out their own directory and group management tasks.
Using a Self-Service portal, users can:
- Search the Directory
- Maintain and Update Their Directory Profiles
- Create and Update Directory Objects, Such As Their Groups
The Self-service portal is a great tool to reduce the workload on IT and helpdesk, since users can create, update, and delete groups on their own. Users can:
- Join and leave groups on their own
- Join and leave groups on behalf of peers and direct reports
- Manually add and remove members from the groups they own
- Manage the memberships, type of members as either temporary or perpetual.
- Create and manage query-based groups for automatic membership update
- Nest groups
- Import and export group members
Administrators, on the other hand, can still maintain complete control over data integrity, since they can define policies and permissions that determine what users can view and change using the portal.
The following screenshot of the GroupID Self-Service portal shows the dashboard for the logged in end-user, and a few useful links to navigate within the portal.
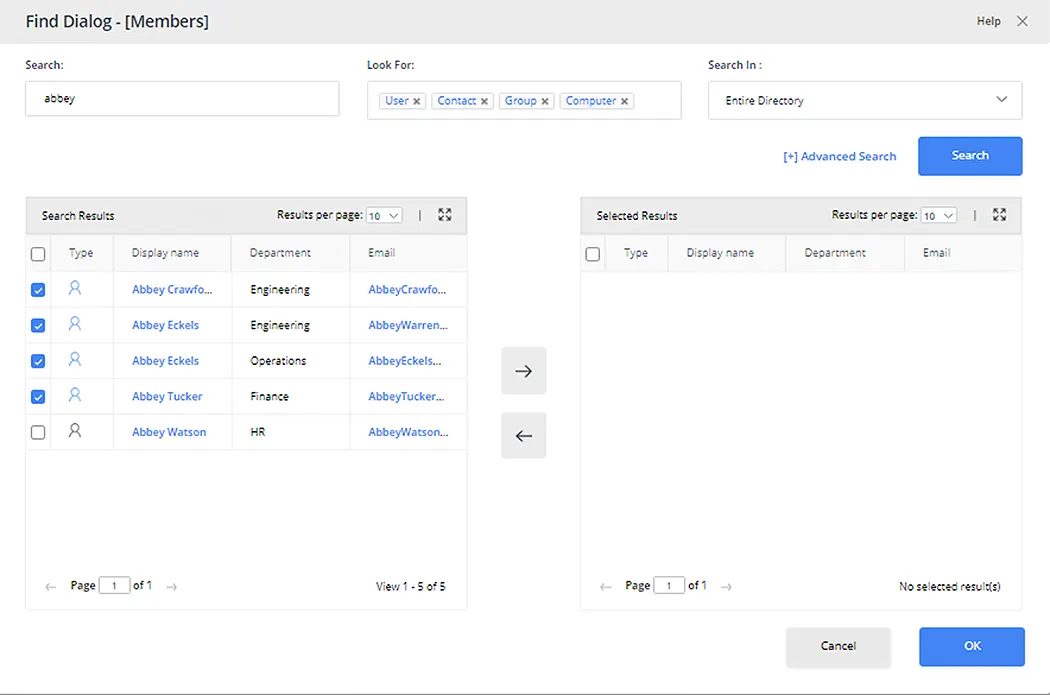
Built-in quick search on the Members tab in group properties lets group owners quickly search for objects and add them as members.
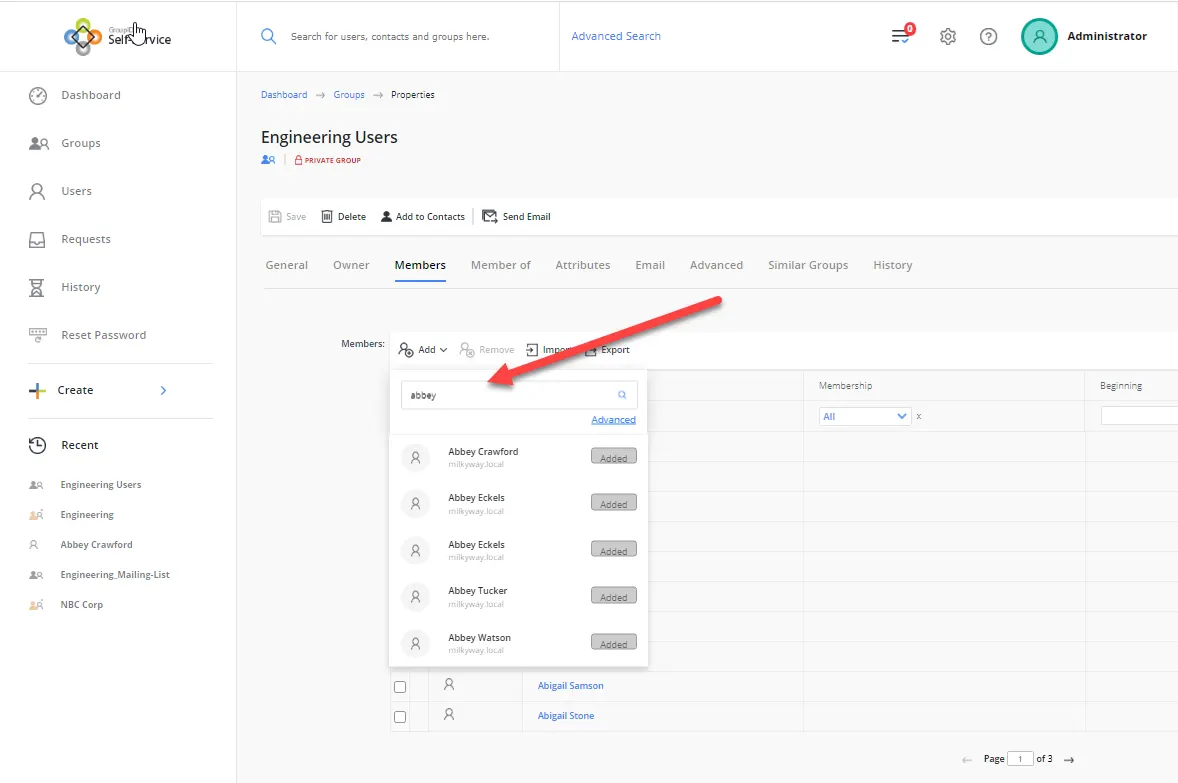
Advanced search gives you more options to narrow down your search, for example:
- The Type of Object to Search
- The Directory OU Where You Specifically Want to Search
- The Facility to Select Multiple Users at A Time to Add To Group Membership
GroupID Management Shell as an Alternative to PowerShell
GroupID Management Shell is a command line interface that enables you to create and manage users, mailboxes, contacts, and groups in Active Directory and Azure AD. You can also create and manage Smart Groups and Dynasties with GroupID Management Shell.
Add-GroupMember in GroupID Management Shell – Description
Same as the Add-ADGroupMember cmdlet, GroupID Shell has the Add-GroupMember cmdlet that lets you add one or more objects to the membership of a group in the directory. Moreover, the cmdlet can be used to perform many other useful group management functions provided by GroupID, such as set the membership type of group members as temporary or perpetual.
Modifying the membership of a Smart Group or Dynasty using this cmdlet is not recommended, since your changes will be discarded the next time the group is auto updated.
GroupID maintains a history for this cmdlet, which you can view in GroupID Management Console.
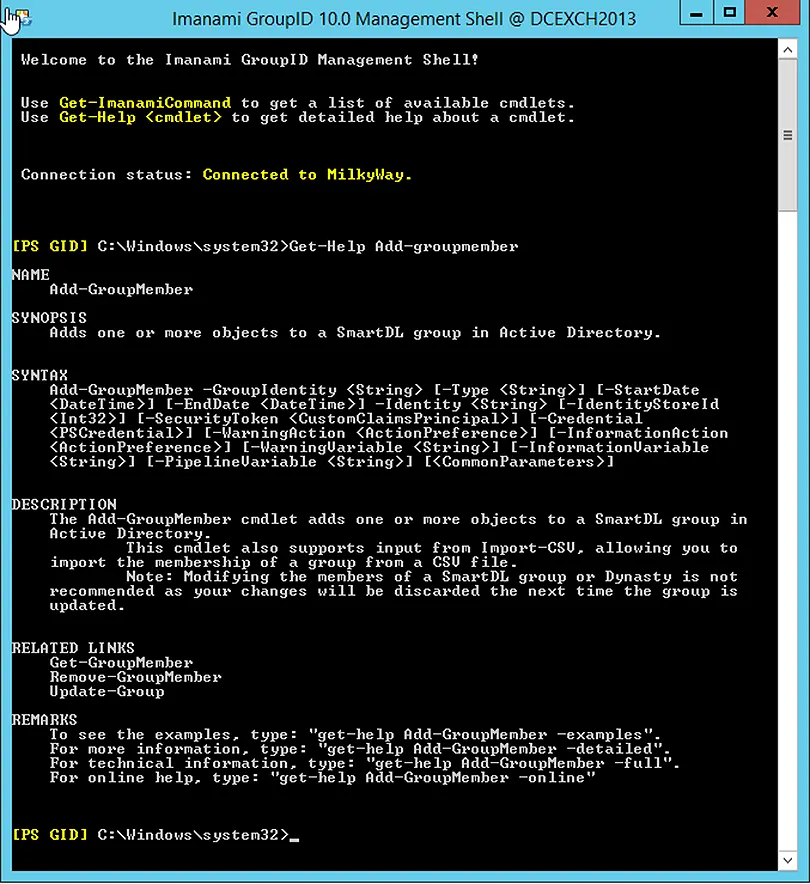
Syntax
The syntax of the Add-GroupMember cmdlet is as follows:
Add-GroupMember -GroupIdentity -Identity [-Type ] [-StartDate ] [-EndDate ] [-IdentityStoreId ] [-SecurityToken ] [-Credential ]
Required Parameters
The main parameters required by the cmdlet are:
- GroupIdentity
- Identity
Summary
We looked into the Add-ADGroupMember cmdlet and its syntax along with common parameters provided to accomplish different scenarios, such as:
- Adding One Or More Users to A Group
- Adding Multiple Users to A Group Using A CSV File
- Adding Multiple Users to Multiple Groups Using A CSV File.
We also looked at how to copy a template group membership to another group. Lastly, we have discussed the need of automating the group membership process using GroupID Automate, the option to delegate group management to group owners using a web-based Self-Service portal, and the benefits of using GroupID Management Shell as an alternative to PowerShell.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.